
10 Minutes
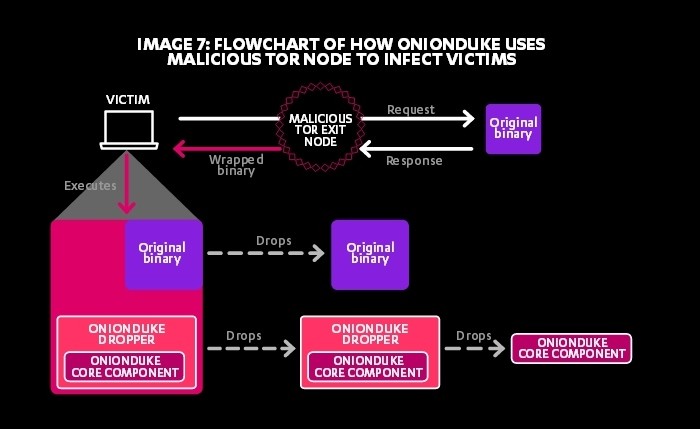
APT29, The Dukes, a term coined by security researchers at Kaspersky Labs, are a well funded, highly resourceful and dedicated group of organized cyber espionage hackers that have been linked to the Russian Federation dating back as far as 2008. Their primary mission traditionally has been to perform intelligence gathering in an effort to support Russian foreign and security policies. The Dukes have access to a vast arsenal of malware toolsets, which have been identified as OnionDuke, CosmicDuke, MiniDuke, GeminiDuke, HammerDuke, PinchDuke, SeaDuke, and CloudDuke to name a few.
The Dukes main cyber weapon of choice is the use of Onion Routing as implemented within the TOR network due to its capabilities for obscuring the identities of the Dukes malicious deeds. The Dukes have recently been engaged in cyber strikes composed mostly of large-scale Spear-phishing campaigns against hundreds upon thousands of targets associated with government organizations and its affiliates. APT29 is probably best known it’s involvement in several attacks against political think tanks in America in addition to public sector organizations and attacks against the Democratic National Committee last year.
APT29 was also implicated in numerous attacks against the State Department, White House, and Joint Chiefs of Staff while CozyDuke was engaged in data mining assaults against the Department of State and White House back the year prior in 2014. The group is best known for exploiting vulnerabilities inherent within the Windows operating system, most pervasively components of the Widows Management Interface among other techniques that took advantage of the “Sticky Keys” feature to help this APT operate under stealth. TOR played a critical role in obfuscating this APTs malicious deeds that when combined with domain fronting, backend encryption, and the use of reflection servers, APT29’s action all culminated in a recipe for disaster.
APT29’s Operation
As far back as 2015, APT29 used “domain fronting” as a process to secure access to backdoors installed on exploited targets. The Russian nation-state group combined the use of TOR’s custom built web browser with a specialized TOR plug-in that implements a domain front to make malicious traffic appear as if it were destined to legitimate websites, such as Google for instance.
Domain fronting is the process of hiding the true nature of traffic from plain sight in addition to obscuring the true identity of the endpoint connection. MEEK, a pluggable transport for TOR, transmits HTTPS requests via a 3rd party server, which is typically a content delivery network or CDN. A CDN consists of a distributed network of proxy servers that are located at multiple data centers world wide. These techniques are most often utilized to bypass online censorship mechanisms such as firewalls.
APT29’s Targets
APT29’s targets are mainly composed of foreign states and government entities that harbor opposing ideologies and political influences to that of the Russian governments. Their latest target was an attack against the Norwegian government including the foreign intelligence, foreign ministry, and others. Nine separate email accounts were involved with a spear phishing campaign. Other targets included the U.S. Presidential election that involved the creation of fake social media accounts that were used to spread fake news in order to persuade voters.
APT29’s Tactics
The APT29 group sets up hidden TOR services in order to establish backdoors in and out of the victim network. After a backdoor has been established, encrypted network tunnels are set up to allow forwarded traffic from the exploited clients to traverse across well know ports 139 (NetBIOS), 445 (Server Message Block), and 3389 (Terminal Services). Using a hidden TOR .onion address, attackers are afforded the freedom of access into and out of the local network.
APT29 leveraged the “Sticky Keys” feature, inherent in the Windows operating system, as a persistence mechanism. APT29’s code essentially replaced the binary files for Sticky Keys with its own version of a customized Windows Command Processor so that when the shift key was pressed five time in succession, a command shell with system level privileges opened. It’s from this command shell that the attackers were able to execute arbitrary Windows commands, including the ability to modify system accounts. Attackers are able to escalate privileges and establish persistent access by tunneling Remote Desktop Protocols or RDP traffic in and out of the system using this well known exploit.

APT29 adopted techniques before they were widely known in early 2015 and prior to any publication thereof.
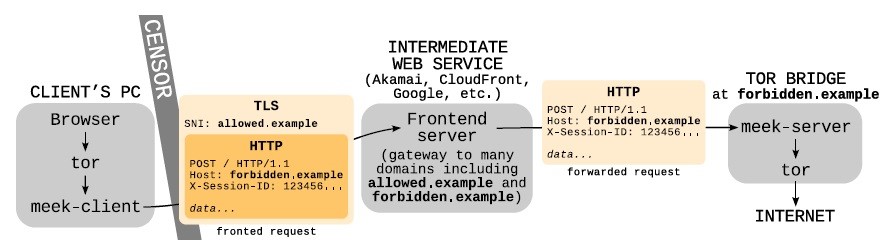
Anti-Detection Mechanism
APT29 utilized the publicly available meek-client plugin to obfuscate TOR connections. Through the use of an intermediate web service, such as a content delivery network, the client submits an HTTP request to the TOR Bridge. The client’s PC obfuscates the legitimate bridge’s domain name of “forbidden.example” from censorship by fronting it with a different name, as provided by the intermediate web service, with in the case “allowed.example. The intermediate service forwards decrypted TLS layer traffic across the bridge in accordance with the original Host’s header then returns data to the client’s PC within the HTTP response. Meek’s client/server architecture is the interface in between the pluggable transport and the TOR browser. All data transmission occurring between meek’s client/server interfaces are impervious to prying eyes. All the while, the legitimate host at “allowed.example” is not participating in the communication event.
The Meek Architecture. (David Fifield, 2015)
Infiltration and Persistence
Attackers executed a script “C:\Program Files(x86)\Google\start.ps1” via PowerShell to activate the “Sticky Keys” exploit and install TOR services after which the script deletes itself. After replacing the “Sticky Keys” binary of “C:\Windows\System32\sethc.exe” with “cmd.exe”, the Windows Command Processor, a privileged console session is accessed prior to system authentication. When the “Sticky Keys” feature is accessed, by pressing the shift key five times in succession, a system-level command shell is opened. This occurs because APT29’s code replaces legitimate system calls to “sethc.exe” with “cmd.exe” that’s linked to the executable which replaced the legitimate “Sticky Keys” binary. Windows service “Google Update” is installed simultaneously during the installation of the “start.ps1” script in order to establish a persistence mechanism.
Domain Fronting
At its most basic level of operation, The Onion Router, aka TOR network, utilizes a series of proxy servers located globally across the Internet where each server, or node, only knows about the previous and next node along the communication’s path. This is know as the minimum 3-Hop feature inherent within the TOR network and where it draws its power to enable communications cloaking. Combined with evasive encryption techniques, the minimum 3-Hop rule makes source tracing of any communication through the TOR network virtually impossible. The obscurity of TOR’s network traffic is what puts it at the forefront of “dark web” traffic, which inadvertently perpetuates criminal activity.
In the past, network analysts most often performed signature analysis as a method of identifying communications associated with TOR’s infrastructure. Enter Meek, an advanced obfuscation plug-in for TOR that’s a publically available application used to enact domain fronting. Meek uses to its advantage routing techniques implemented by CDNs and Google. CDNs operate by routing traffic associated with an IP address for one service to a server associated with a different hosted service within the same network. Meek accommodates TOR’s communication obfuscation by hiding traffic inside legitimate HTTPS connections of well-known services by using reflection servers hosted inside of a CDN.
Meek’s obfuscation process occurs in several stages. TOR encodes HTTP traffic with a specified reflection server’s host name, i.e. meek-reflect.appspot.com. The HTTP traffic is then wrapped inside of a legitimate TLS link to a hosted server that resides on the same CDN cloud acting as the reflection server, i.e. Google. The CDN decrypts the connection once it receives the TLS traffic, which reveals the hostname in the HTTP header then forwards the corresponding traffic to the reflection server. The original HTTP stream’s TOR traffic is reconstructed by the reflection server and forwarded to the TOR network after which it’s routed to its final destination.
MEEK Traffic Flow. (Dunwoody, 2017)
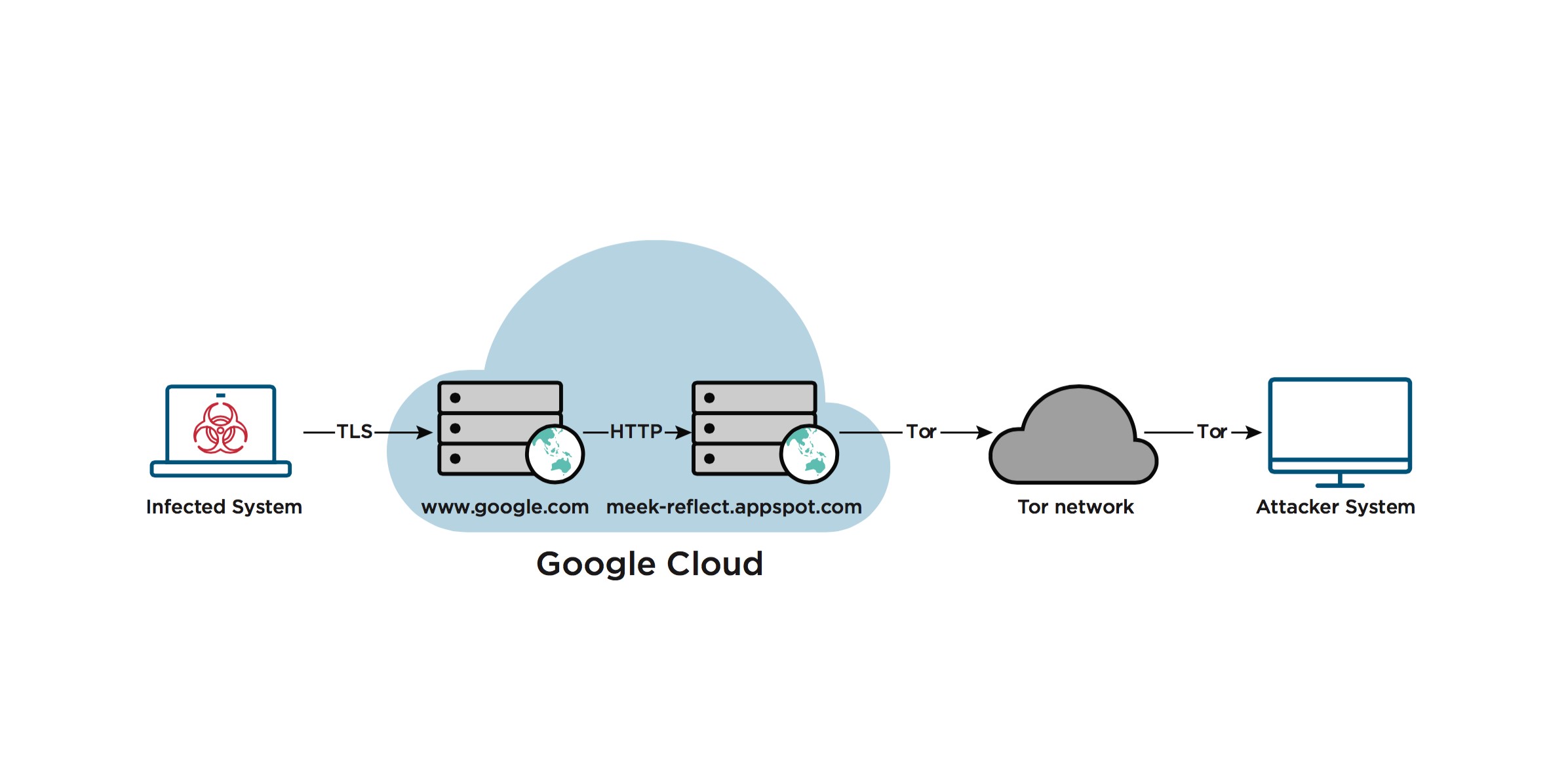
This process is what creates an outbound network connection appearing to contain legitimate HTTP POST requests targeted at google.com on a Google registered IP address allowing traffic to pass through the reflection server discretely onto the TOR network. It must be noted that Google suspended the meek-reflect.appspot.com reflection server but other CDN supported reflection servers yet still fulfill the same functions.
APT29’s Motivations
APT29’s activities are deemed to be closely associated with the Russian Civilian and Military Intelligence Service, aka RIS, whose actions are politically motivated. Actions by the RIS are a part of an ongoing campaign whose cyber activities are mostly aimed at the United States and its citizens. Many of these cyber operations included phishing campaigns directly aimed at disrupting American infrastructure and its interests including, Universities, political organizations, think tanks, government organization, and theft of corporate information.
Mitigation Strategies
Mitigation of Russian APT group’s cyber threats require a commitment on behalf of all responsible parties to abide by cybersecurity best practices, which is integral to protecting critical infrastructure. There are a wide variety of techniques that can be implemented at all levels of an organization that help mitigate these threats including the following:
- Backups: Is there a backup/recovery plan in place? Has it been tested? Are there any warm/hot/cold site requirements?
- Risk Analysis: Has the organization undergone a risk assessment? What vulnerabilities need to be addressed?
- Personnel Training: Are there any social awareness programs?
- Scanning & Patching: Has the network undergone any type of penetration testing? What kinds, black/white/grey box testing?
- Application Whitelisting: Are only approved trusted application allowed to run?
- Incident Response: Is there an Incident response plan in place? Has it been tested?
Conclusion
APT29’s tactics, techniques, and procedures (TTPs) were adopted by them before they became widely known. Through the utilization of publically available infrastructure, APT29 was able to harness the full power of obfuscation through obscurity using a wide set of tools to hide their network traffic with the use of minimal research and/or development, making the difficulties involved with attribution greater.
A key component to detecting these kinds of activities is to ascertain visibility into TLC connections and network signatures associated with traffic. Effective endpoint visibility is essential when dealing with APT groups who are capable of utilizing rapidly developing methodologies that capitalize on obscured network traffic. Having the ability to monitor events from a multitude of attacker methodologies, as in the creation of new persistence mechanisms or lateral movements, has the potential to help network defenders reveal these stealthy methods.
Although attribution is made more difficult by the methods employed by the Dukes, learning about how they operate using the methods discussed can help network defenders establish fingerprints in association with motives behind future cyber attacks.
References
Brook, C. (2017, 3 27). APT29 Used Domain Fronting, Tor to Execute Backdoor. Retrieved from ThreatPost: https://threatpost.com/apt29-used-domain-fronting-tor-to-execute-backdoor/124582/
David Fifield, C. L. (2015). Blocking-resistant communication. Retrieved from Academics at the University of California Berkeley: http://www.icir.org/vern/papers/meek-PETS-2015.pdf
Dunwoody, M. (2017, 3 27). APT29 Domain Fronting With TOR. Retrieved from FireEye: https://www.fireeye.com/blog/threat-research/2017/03/apt29_domain_frontin.html
FSLabs. (2014, 11 14). OnionDuke: APT Attacks Via the Tor Network. Retrieved from F-Secure Labs: https://www.f-secure.com/weblog/archives/00002764.html
Labs, F.-S. (2015, 9 15). THE DUKES 7 years of Russian cyberespionage. Retrieved from f-secure.com: https://www.f-secure.com/documents/996508/1030745/dukes_whitepaper.pdf
MITRE. (2017, 5 1). Group: APT29, The Dukes, Cozy Bear. Retrieved from ATT&CK: https://attack.mitre.org/wiki/Group/G0016
Paganini, P. (2017, 2 17). Russian APT 29 group launched cyber attacks against Norwegian authorities. Retrieved from securityaffairs.co: http://securityaffairs.co/wordpress/55958/apt/apt-29-group.html
Discover more from Decentralized Intelligence
Subscribe to get the latest posts sent to your email.