6 Minutes
The proliferation of USB devices not only is an added convenience to users but also a hindrance to network and information security and as a result can be used for nefarious purposes. This is why having the ability to examine USB device history and files are critical to digital forensic investigations. This assignment will walk through the basic forensic examination process of how to examine USB drive artifacts.
This assignment was performed using Windows 10 running as a virtual machine inside of VMware Fusion 8 hypervisor on macOS Sierra as the host operating system. The first step is to wipe the hard drive clean in order to achieve uncontaminated results during our experiment. After a short search, I decided to use a freeware program called “Disk Wipe v1.7”. For the sake of time, I decided to wipe the USB drive using the one pass zero option, which basically write a pattern of zeroes across the entire drive’s files system ensuring that no remnants of any prior data remains.
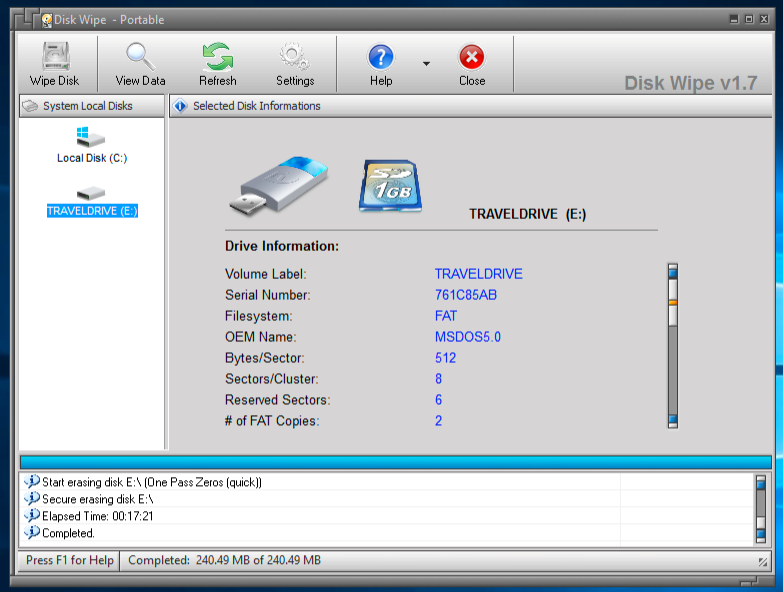
Figure 1
Step two is to ensure that we have a forensically sound environment by enabling USB write block, which I had performed using a quick registry hack as seen below in figure 2.
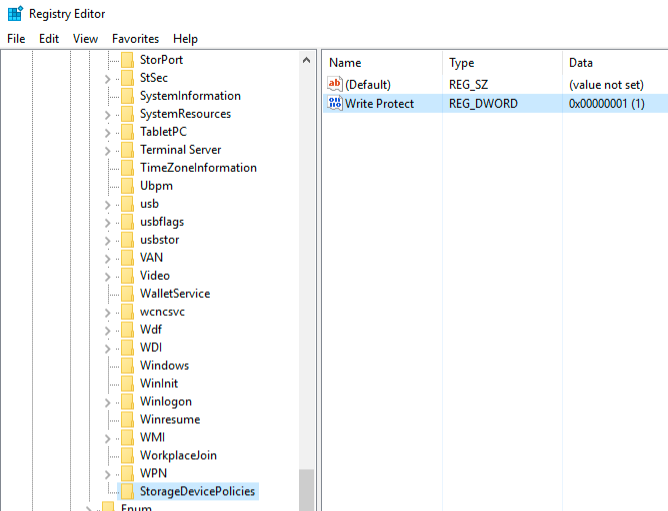
Figure 2
Next, I performed physical acquisition using FTK Imager as seen in figure 3 below. The hash and details of the forensic image acquisition is displayed as well in figure 3. NOTE: MD5 and SHA-1 Hashes were performed simultaneously providing two hash values adding an extra layer of integrity checking.
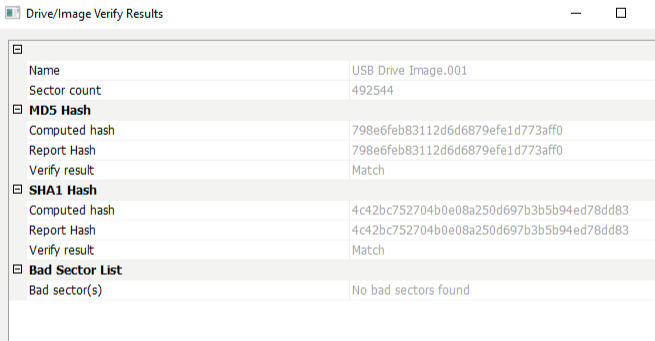
Figure 3
Below is the Image Summary output from FTK Imager, which is a more detailed data output.
Created By AccessData® FTK® Imager 3.4.3.3
Case Information:
Acquired using: ADI3.4.3.3
Case Number: 123
Evidence Number: 456
Unique description: USB image
Examiner: miguel
Notes:
————————————————————–
Information for C:\Users\mbigueur\Desktop\USB Drive Image:
Physical Evidentiary Item (Source) Information:
[Device Info]
Source Type: Physical
[Drive Geometry]
Cylinders: 30
Tracks per Cylinder: 255
Sectors per Track: 63
Bytes per Sector: 512
Sector Count: 492,544
[Physical Drive Information]
Drive Model: Memorex TD 2C USB Device
Drive Serial Number: 28816C40239208F0
Drive Interface Type: USB
Removable drive: True
Source data size: 240 MB
Sector count: 492544
[Computed Hashes]
MD5 checksum: 798e6feb83112d6d6879efe1d773aff0
SHA1 checksum: 4c42bc752704b0e08a250d697b3b5b94ed78dd83
Image Information:
Acquisition started: Sat Apr 08 12:04:28 2017
Acquisition finished: Sat Apr 08 12:05:06 2017
Segment list:
C:\Users\mbigueur\Desktop\USB Drive Image.001
Image Verification Results:
Verification started: Sat Apr 08 12:05:07 2017
Verification finished: Sat Apr 08 12:05:10 2017
MD5 checksum: 798e6feb83112d6d6879efe1d773aff0 : verified
SHA1 checksum: 4c42bc752704b0e08a250d697b3b5b94ed78dd83 : verified
I then created ten test files as seen below in figure 4 and copied them to the USB drive.
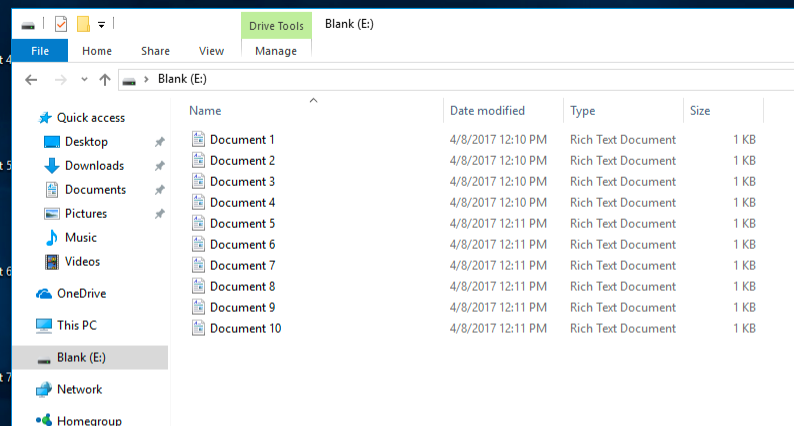
Figure 4
The new hash values for the USB drive after adding the ten files are seen below in figure 5. It should be noted that both of the MD5 and SHA-1 hash values have changed subsequent to the addition of the aforementioned ten files.
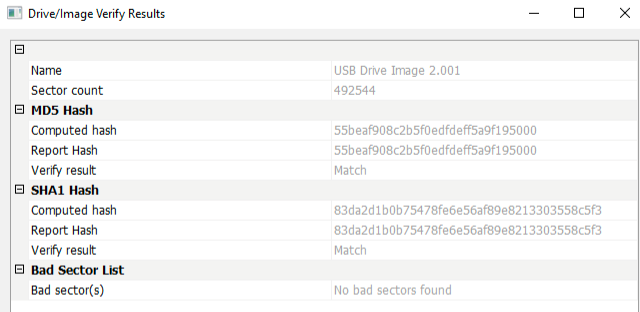
Figure 5
Below is the output from the Image Summary screen from FTK Imager revealing more details of the drives metadata.
Created By AccessData® FTK® Imager 3.4.3.3
Case Information:
Acquired using: ADI3.4.3.3
Case Number: 112233
Evidence Number: 445566
Unique description: 2nd image
Examiner: miguel
Notes:
————————————————————–
Information for C:\Users\mbigueur\Desktop\USB Drive Image 2:
Physical Evidentiary Item (Source) Information:
[Device Info]
Source Type: Physical
[Drive Geometry]
Cylinders: 30
Tracks per Cylinder: 255
Sectors per Track: 63
Bytes per Sector: 512
Sector Count: 492,544
[Physical Drive Information]
Drive Model: Memorex TD 2C USB Device
Drive Serial Number: 28816C40239208F0
Drive Interface Type: USB
Removable drive: True
Source data size: 240 MB
Sector count: 492544
[Computed Hashes]
MD5 checksum: 55beaf908c2b5f0edfdeff5a9f195000
SHA1 checksum: 83da2d1b0b75478fe6e56af89e8213303558c5f3
Image Information:
Acquisition started: Sat Apr 08 12:15:10 2017
Acquisition finished: Sat Apr 08 12:15:48 2017
Segment list:
C:\Users\mbigueur\Desktop\USB Drive Image 2.001
Image Verification Results:
Verification started: Sat Apr 08 12:15:48 2017
Verification finished: Sat Apr 08 12:15:51 2017
MD5 checksum: 55beaf908c2b5f0edfdeff5a9f195000 : verified
SHA1 checksum: 83da2d1b0b75478fe6e56af89e8213303558c5f3 : verified
Figure 6 below is the hashed output of all ten files resident on the USB drive.
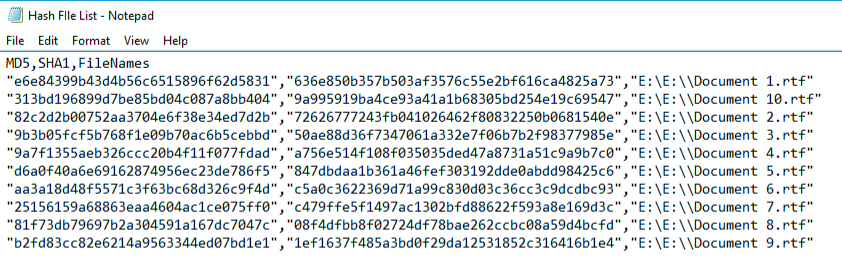
Figure 6
Figure 7 below shows a snapshot of what the files look like using FTK Imager.
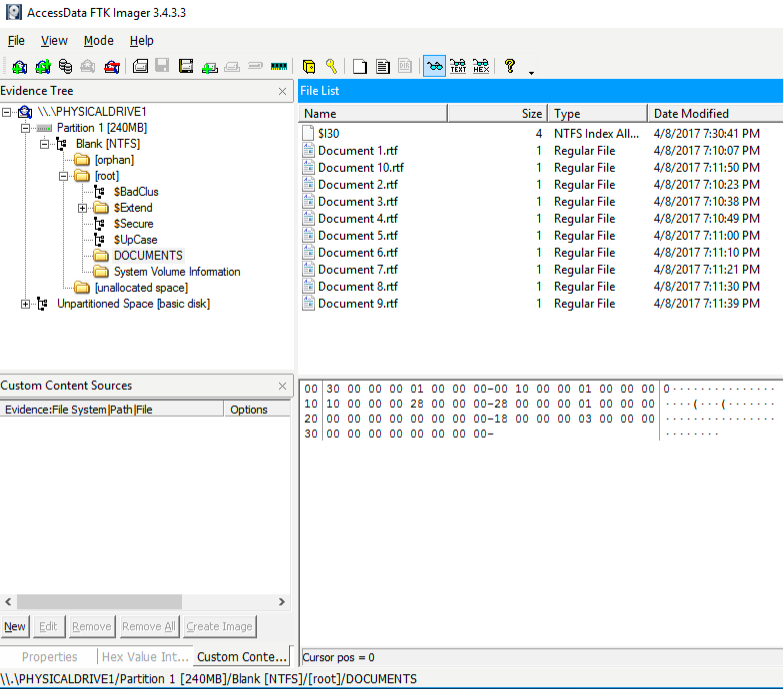
Figure 7
In figure 8 below, FTK Imager was able to retrieve file artifacts for all ten files after they have been deleted as referenced by the red X. The contents of Document 10.rtf are displayed in the lower right window.
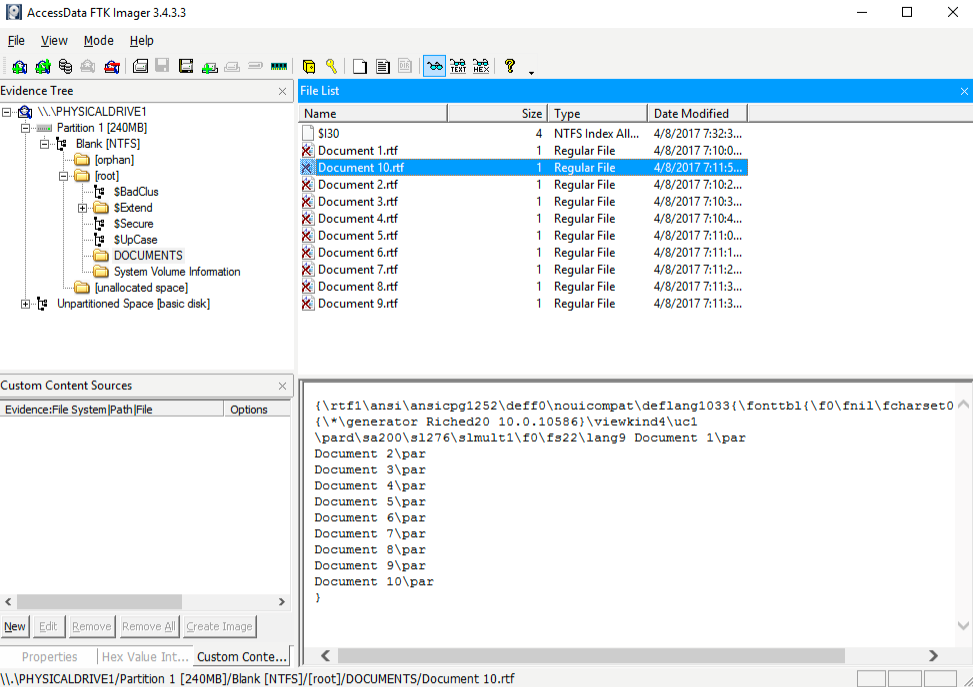
Figure 8
Figure 9 reflects the contents of the original file Document 10.rtf.
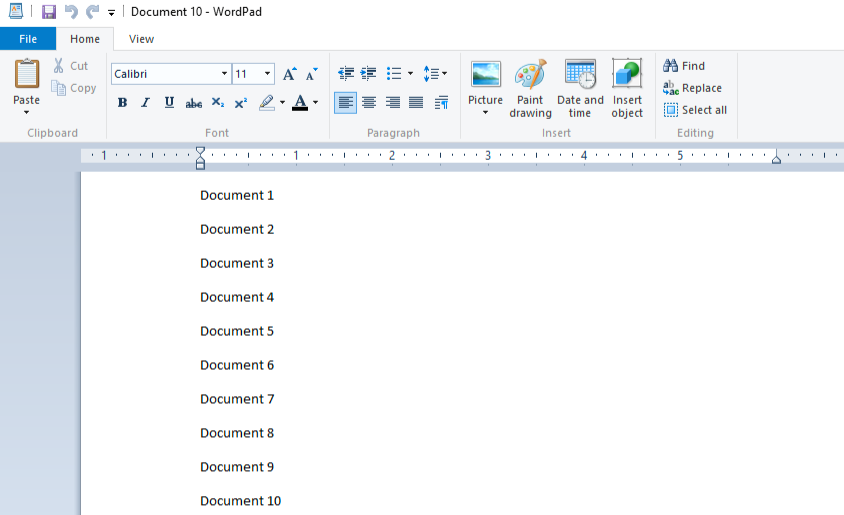
Figure 9
Follow up Questions
What is the difference between physical and logical acquisitions?
- A physical acquisition is the collection of all ones and zeros present on the USB drive as opposed to a logical acquisition, which is the collection of active data as contained in the file system.
What is the difference between wiping and formatting a drive?
- Formatting a hard drive simply deletes the shortcuts to the resident files on the drive making the sector appear to be available to be written to by new data. This makes data recovery possible after deletion.
- Wiping a hard drive or “Disk Scrubbing” or “ Disk Sanitation” is the process of writing new data over the old data making it difficult if not possible to recover. This can be done using several standards such as writing all 0’s or alternating 0’s and 1’s in addition to writing over the entire drive several times as is the case with the government standard disk sanitation process.
How do you know if a USB device is “unique” based on the serial number? Is the one that you utilized in your assignment a unique USB device?
- The format of the serial number will identify whether the USB device is unique or not on a per manufacturer basis. Device serial numbers are considered unique values by many security practitioners with the small exception of a piece of software called PB Downforce, used mainly within the gaming community to spoof device ID’s for gamin purposes.
Where in the Windows Registry will it show information about the USB device you connected to your computer? Can you show this on your machine?
- HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Enum\USB\<hardware id>\<instance id>\Device Parameters
- This can be shown on my machine by running the regedit program and performing a string search.
What pertinent USB information can be found in the setupapi.dev.log file?
- Installation events, device and driver installation information.
Explain the following USB Artifacts:
- VID/PID
- The Vendor ID is an alphanumeric value, which indicates the manufacturer of the device.
- The Product ID is a specific numeric value that indicates product device information.
- Volume GUIDProduct ID
- The GUID Product ID is the principle identification of a product or application. Typically used to represent the version of a product as a trigger for future updates if required.
References
InfoTrendSec. (2015). Erasing All the Data: Format vs. Disk Wipe. Retrieved April 8, 2017, from http://www.infotransec.com/blog/2013/06/18/erasing-all-data-your-hard-drive-format-vs-disk-wipe
Coons, P. (2014, December 9). 3 Methods of Forensic Imaging. Retrieved April 8, 2017, from http://d4discovery.com/discover-more/3-methods-of-forensic-imaging#sthash.xcyHKUiT.dpbs
Ross, A. (2012, April 23). USB Flash drive Serial Numbers – “UNIQUE”? Retrieved April 8, 2017, from http://digfor.blogspot.com/2012/04/usb-flash-drive-serial-numbers-unique.html
Microsoft. (2017). USB Device Registry Entries. Retrieved April 8, 2017, from https://msdn.microsoft.com/en-us/library/windows/hardware/jj649944(v=vs.85).aspx
Microsoft. (2016, January 30). SetupAPI Logging. Retrieved April 8, 2017, from https://msdn.microsoft.com/en-us/windows/hardware/drivers/install/setupapi-logging–windows-vista-and-later-
Microsoft. (2016, July 30). Device Unique Identifiers (DUIDs) for Storage Devices. Retrieved April 8, 2017, from https://msdn.microsoft.com/en-us/windows/hardware/drivers/storage/device-unique-identifiers–duids–for-storage-devices
Microsoft. (2017). ProductCode property. Retrieved April 8, 2017, from https://msdn.microsoft.com/en-us/library/windows/desktop/aa370854(v=vs.85).aspx
Discover more from Decentralized Intelligence
Subscribe to get the latest posts sent to your email.