7 Minutes
The biggest names in U.S. media and brand name advertising are losing millions in advertising dollars on a dally basis due to a Russian underground of cyber criminals. This operation in particular targets video ads by producing massive volumes of fraudulent video ads through the misappropriation of various parts of critical Internet infrastructure then targeting premium-advertising space. As revealed by security experts, a new and very successful click fraud, as perpetrated by Russian cyber miscreants, has resulted in the loss of millions of dollars on a day-to-day basis.
Although the lone group of Russian misfits operate out of Russia, they controls that extends far beyond their borders and oceans by controlling malicious web browsers installed on web servers harbored within legitimate data centers located mainly in the U.S. and Netherlands. This global botnet farm tricks advertising networks into believing that real human beings are viewing hundreds upon millions of video ads daily. Methbot’s Russian cyber syndicate controls these data centers by acquiring troves of legitimately owned Internet service provider IP addresses then creating fake documents claiming the rights to using them at which point they given the authority to access video ads through the use of a custom web browser.
Through the leveraging of programmatic digital ad bidding networks, the Methbot Russian crime syndicate takes in millions of dollars daily by impersonating publishers and convincing advertisers that real people are actually watching their ads.
The Methbot Operation
Targets – The Advertising Ecosystem
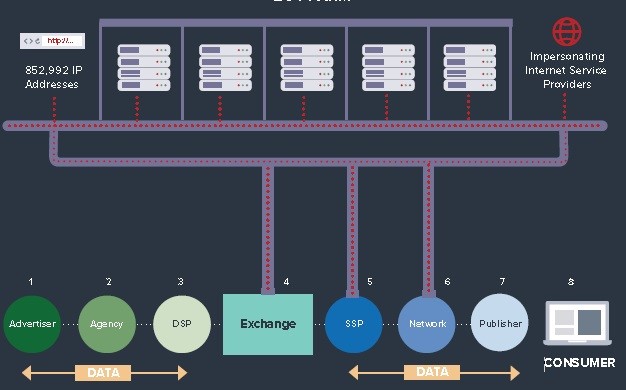
The advertising universe is composed of many moving parts all working together to forge the ecosystem as it’s known today. The parts all culminate to serve two singular purposes, that of supply and demand, which in digital advertising relies on digital advertising, thus, its heavy reliance on technology. Technology designed to facilitate the interchange of information between the two sides of advertising, the advertisers (Demand), and the publishers (Supply), has become integral in the day-to-day operations of this ecosystem.
The Advertisers
Advertising agencies acting on behalf of their customer base, the advertisers manage the planning and execution of marketing plans designed to provide the highest quality possible of targeted ads to its consumer base. Demand Side Platforms or (DSPs) are technology-based platforms that mange the interconnection of programmatic exchanges and publishers alike to discover its targeted audience on the supply side. From time to time, in order to realize the highest rate of return against their media plan, advertisers will establish a targeted demographic data pool in an effort to identify premium inventory inside the private marketplaces or PMPs.
The Publishers
The Supply Side Platform or (SSP) is a technology platform designed to enable web publishers to manage their advertising space inventory. (Wikipedia, 2017) It is used to acquire audience inventories from publishers and networks to DSPs who perform bidding within the exchange. Publishers and SSPs establish premium segments of inventory and audiences to meet the specific needs of advertisers. At the conclusion of the auction, the highest bid wins then the ad is loaded and viewed by the consumer on the content they are accessing, which appears to come from the spoofed advertiser.
The Advertising Ecosystem Basics (WhiteOps, 2016)

Methbot Tactics
Avoidance. As part of the Methbot avoidance detection process, the group cultivated an assortment of dedicated infrastructure by distributing their operations across a network based, customer browser engines strategically located in data centers running on legitimate server IP addresses that were acquired using spoofed data from legitimate registrations. These forged IP registrations is what allowed the Methbot operation to evade modern day detection methodologies and fly under the radar of layered defense systems including, firewalls, intrusion prevention systems, and security event managers or SEIMs. The Methbot operation was acknowledged an innovation in botnet technology by transcending beyond the capabilities of other traditional botnets, thereby, placing it in its own class of bot fraud.
Infiltration
Methbot is motivated by the high demand of both premium publisher content and human demand. Methbot fulfills the needs of advertisers by supplying massive amounts of fake audiences from highjacking the brand power of prestigious publishers by using falsified inventory and spoofed domains in return allowing Methbot to siphon away millions in genuine advertising dollars.
Methbot process
- Masquerade as established site using fabricated inventory.
- Operate on a dedicated custom-built desktop browser.
- Utilize fake social network logins and mouse movements.
MethBot Farm Operation (WhiteOps, 2016)
The Human Masquerade
Due to advertiser’s reliance on cookies residing on user’s machines, which contain targeted advertising demographics such as, purchase history, browser history, etc., Methbot operators take advantage of this by using crafted cookies and placing them into fake web sessions by leveraging software contained within well known open source libraries to establish persistent identities that contain information seen as valuable to advertisers. This is the hook that tempts high paying advertisers to spend top dollar on perceived commodities of precise targeted audiences.
Methbot operators also leveraged fake cursor movements and mouse clicks to mimic human behavioral trends in an attempt to depict a more convincing forgery of human behavior. Adding to this sophistication, Methbot utilizes fake social network login data in an effort to appear as a users logged in during the occurrence of an ad impression.
Motivations
In the simplest terms, money is what motivates the Methbot operators. They are a technology based crime syndicate organized around the inceptives of stealing money by means of selling fake advertising data.
Volume and Estimated Financial Impact
- Revenue streams between $3 to $5 million dollars daily.
- 200 – 400 million video ad impressions generated daily on fabricated inventory.
- 250,267 distinct spoofed URLs used to falsely represent inventory.
- 6,111 targeted and spoofed premium domains.
- High value targeted marketplace.
Mitigation Techniques
The Methbot operators were able to exploit the entire digital advertising marketplace due to the resulting anonymity of online advertising and resulting complex interconnectivity. Ad impressions, at any point in time, most often passes through many hands prior to landing on a page where the ad is served. Tracing back to the point of origination for each ad impression is not economically viable due to limitations set forth upon the human capital involved in doing so, in addition to the difficulties involved with walled gardens, reselling, and competing interests.
An aligned response from the industry to establish close relationships between advertisers and publishers could help circumvent many of the obfuscation attempts made by Methbot by increasing transparency, thus, making it difficult for advanced bot operations like Methbot from taking advantage of a closed and mostly impervious system as it exists today. The industry as a whole can display a show of vigilance by closing ranks against any threat by increasing transparency for all across the advertising spectrum.
Conclusion
Methbot to date is the largest and most profitable digital online add fraud operation to date. Russian cyber criminals are tapping into a multi million-dollar industry by stealing advertising dollars away from U.S. media companies and advertisers. With an army of automated web browsers, using fraudulently obtained IP addresses, Methbot watches as many as 300 million video ads on fake websites per day designed to appear like premium publisher content. Methbot is fluid and has the capability to adapt to network defenses through code based mutation and/or the reacquisition of new revenue based targets when blocked.
By realigning supply and demand interests, the industry has the capability to increase transparency and reduce obfuscation therefore making it increasingly difficult for even the most advanced operations like Methbot to succeed.
References
Colón, M. (2016, December 20). Russian Cybercrime Group Nets $3 to $5 Million A Day in ‘Methbot’ Ad Ruse. Retrieved from misti.com: http://misti.com/infosec-insider/infosec-news-in-a-minute/russian-cybercrime-group-nets-3-to-5-million-a-day-in-methbot-ad-ruse
WhiteOps. (2016, December 2016). The Methbot. Retrieved from Whiteops.com: http://www.whiteops.com/methbot
Wikipedia. (2017, September 15). Retrieved from https://en.wikipedia.org/wiki/Supply-side_platform
Discover more from Decentralized Intelligence
Subscribe to get the latest posts sent to your email.