20 Minutes
Computer networks are more advanced today than ever. More and more users are demanding greater access to these systems and as a result administrators are tasked with the dilemma of securing these highly complex networks. Many systems at one time had the luxury of relying on basic firewall implementations, which consisted of IP filtering and port blocking. In todays society this is no longer an option.
As today’s computer network systems advance, so do the intruder’s methods who wish to wreak havoc upon them. One such advancement in network security is the implementation of an IDS/IPS (Intrusion Detection System/Intrusion Prevention system). An IDS/IPS is a great addition to any unified threat management system, which can help thwart off an attacker’s advance or slow them down long enough to initiate alternative security measures. This paper will also explore the costs savings of outsourcing computing resources in conjunction with the security benefits and/or security vulnerabilities associated with doing so.
Recommendation & Justification
As illustrated in the drawing, the Linux IP Tables firewall is the first line of defense but doesn’t go far enough to protect the network. The two Gigabit Ethernet switches were added at minimal costs to help segment the network into two smaller branches that can be easier to manage. This allows access controls to be implemented effectively and also helps eliminate network congestion at choke points. Building systems capable of lower throughput management is more cost effective in this case. I would place one IDS/IPS system directly connected to the default gateway router.
Adding a single IDS system with a direct connection to the router enables all inbound and outbound traffic to be monitored on the WAN and LAN interfaces. This is the most cost effective implementation based on the amount of bandwidth the servers will be utilizing. Placing the IDS/IPS system on a separate router interface at the Default Gateway will not affect the network if the IDS/IPS were to fail. I think mitigating the costs of a massive cyber-attack is enormous compared to the costs of securing a network.
For any business to remain viable in today’s global economy, one has to take into consideration the costs of doing business online especially if e-commerce is involved. Even brick and mortar stores are vulnerable to cyber-attacks because they have to maintain an online presence to stay competitive in today’s business environment. There are many more convenient vulnerabilities for crackers to exploit as a result of finding new ways to make doing business more convenient for the consumer .
Network Segmentation – VLANS
Segmenting the network into separate VLAN domains adds additional layers of security. VLANs segregate traffic based upon application specific functions and create a smaller attack footprint for crackers thus isolating breaches and minimizing any potential casualties. Two VLANs will be used in this design, one as the outer or serving VLAN and one as the inner or private VLAN, which essentially establishes a protected enclave. Protected enclaves are based on a defense-in-depth architectural approach to design and serve as an integral part of any unified threat management system. Within the enclave are a whole variety of servers including, email, print, file, and application servers, which are designed for interdepartmental use. These servers are contained within a protected zone behind a firewall designed to filter traffic. VLAN 25, which is the outer VLAN, is added to the server’s Gigabit Ethernet switch’s promiscuous port facing the default Gateway Router. Internal private VLANS 22, 23, and 24 segregate network traffic based on specific application use establishing three separate broadcast domains. Segmenting broadcast domain helps reduce latency across the servers increasing throughput and adding an extra layer of security. VLAN 27 connects the workstation’s Gigabit Ethernet Switch’s promiscuous port to the default Gateway. Internal VLAN 26 establishes a single broadcast domain for all internal workstations.
Protected Enclave
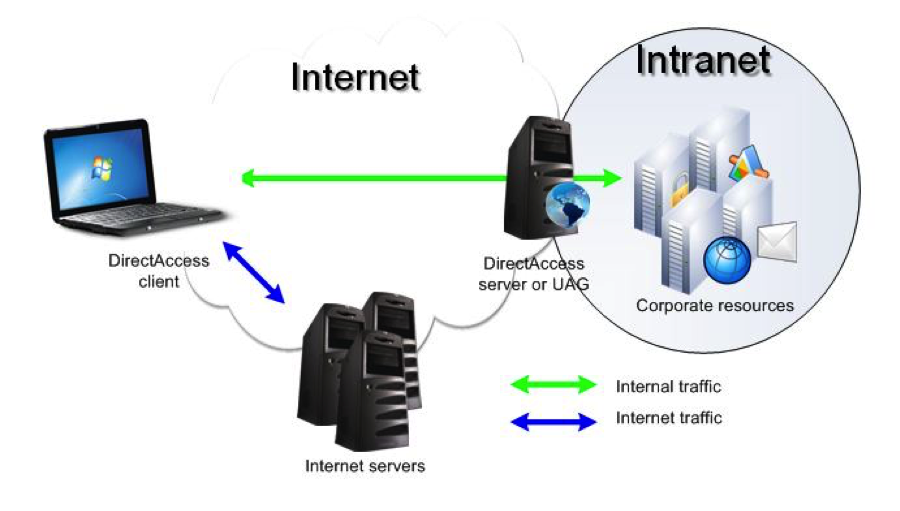
A protected enclave can be considered an intranet. These particular networks are subdivided into smaller sub networks, which are typically arranged by organization and departmental needs. This somewhat helps eleviate the dilemma faced with providing security for one giant network. Protected network enclaves are based on a defense-in-depth architectural approach to design. Protected Enclaves are seen as a corporate productivity tool, which typically restricts employees to a particular organization or department. Security breaches are less likely to affect protected enclaves that belong to different IP networks. Within the enclave is whole variety of servers including, email, print, file, and application servers, which are designed for interdepartmental use. These servers are contained within a protected zone behind a firewall designed to filter traffic.
Upon successful authentication, a VPN link is established remotely into the enclave allowing the authenticated user to access files and applications based upon access privileges. Web servers are typically deployed within protected enclaves, which provides organizational members access to internal websites. Any viable protected enclave will have an Intrusion detection system deployed within the protected Zone. Protected Enclaves are scalable, have many different uses, and add an essential layer of security. Appropriate security policies must be in place in order for protected enclaves to be effective by design.
Web Servers
The intranet web server is placed within the DMZ on VLAN 22. The DMZ is part of the protected enclave fed from the 10GIG uplink. The intranet servers should be located inside of a secured facility with proper access privileges in place. Limiting access to authorized individuals only helps ensure computers and/or devices are not physically compromised. Sensitive webpages should be encrypted with SSL. SSL encrypted web pages allows organizational employees to view sensitive data over a secured connection such as 401Ks and payroll information.
Network Security
I think that it’s a good idea to check for suspicious activity at regular intervals during the day. Doing more is better than doing less. Business networks are typically busier during normal business hours, thus the perfect cover for an attacker to put on their masquerade, so it only makes sense to schedule a more intense security audit routine around normal business hours. The days of solely relying on the security net provided by placing a firewall between a secured network and the world are no longer sufficient. Deploying a Unified Threat Management system is the new norm but still does not go far enough. With the advent of mobile computing, a whole new dynamic of defense mechanisms must be developed and deployed at each outlet. In today’s business world, mobile computing is a necessity to stay connected while having instant access to information, which helps boost business productivity. Being efficient in developing and deploying good security policies brings about a whole new defense dynamic. Security policies need to constantly accommodate network changes and continuously adapt to new evolving security threats.
Web Server Security
Java is the biggest single threat to PC security in today’s society. Just for the mere fact that Java runs on almost every electronic device large and small makes it an easy target for crackers. It doesn’t help when almost half of the users are not running the most recent patched Java version. Users could potentially load unsafe resources carrying malicious Java code. Each new version of Java introduces exploited vulnerabilities faster than most users care to keep up with. Running the latest Java update patch seems to be a hindrance to most; therefore, security typically takes a back seat and becomes an afterthought. Java has a long way to go before it solves its ongoing security issues. Java makes it known their software runs on over 3 billion devices worldwide. That’s a huge footprint for crackers to exploit. Oracle makes it well known that updating Java instantly after a security patch becomes available is critical to maintaining a secure network. Does it really though? Oracle’s latest security advisories indicated 14 fixes for Java software.
“Updates are released quarterly in January, April, July and October. Unfortunately, Oracle continues to periodically receive reports of active exploitation of vulnerabilities that have already been fixed by Oracle in previous Critical Patch Update releases,” said Maurice. Dan Worth, v3.co.uk
Users need to be keen on checking for the SSL Lock icon in the URL making sure it’s green and not yellow with a caution sign. Unfortunately, SSL lock icons are very tiny and don’t really stand out very well visually. I have seen some locks that have thick heavy green highlights, which are easy to see and stand out very well. I’ve also visited websites where there is no icon whatsoever and typically URLs do indicate HTTPS.
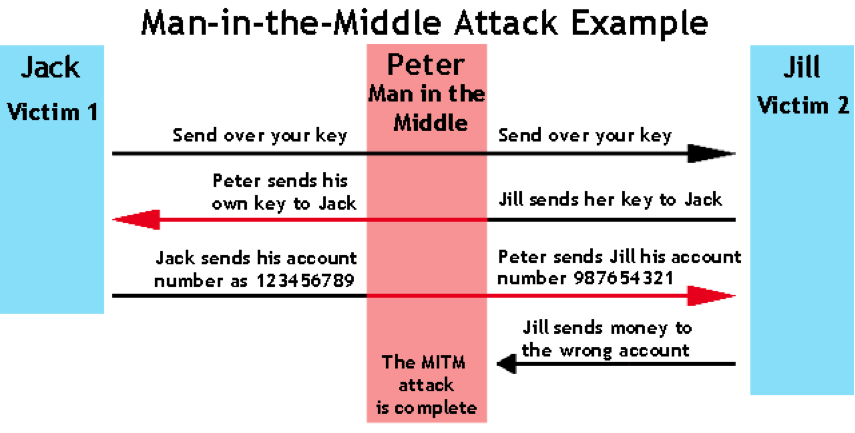
Besides man-in-the-middle attacks, other types of attacks that could potentially exploit HTTPS are the vast number of certificate authorities that exist. Crackers only need to fool a single certificate authority, which could propagate to many other certificate authorities spreading malicious code. Many certificate authorities do not perform due diligence when issuing certificates, consequently, a lack of confidence from the public has ensued. Certificate issuing authorities could potentially be compelled to issue phony certificates. Past HTTPS exploits include the “Heartbleed Bug” and most recently the “Freak Attack”.
DNS Poisoning
One measure a user could take to ensure their local hosts file is accurate is to keep their resolver private and protected if they own their own resolver. This enables the administrator to have authority over local user restrictions reducing the chances of a cracker attack from outside the organization poisoning the DNS resolver. Administrators could also limit their trust relationships with other DNS servers. Using the most recent version of DNS BIND can help eliminate vulnerabilities inherent in outdated versions. The Measurement Factory has a nice tool to check for open resolvers on networks. “DNS Measurement Factory”.

Another option is to manage your DNS servers securely. DNS servers can either be hosted by users or hosted by a service provider. Possible ways of preventing a cracker from getting bogus responses accepted is to use random source ports or randomizing query IDs. Also, randomizing case letters in the site names will help because valid name servers will reply with the exact same case letters. For example, GoFiShinG.com will return GoFiShinG.com from a valid name server instead of gofishing.com. It’s also a good idea to ensure, if possible, that DNS servers have DNSSEC deployed. DNSSEC helps determine whether an organization’s public-key cryptography can be trusted or not. DNSSEC also ensures that user’s computers are aware of DNS records pointing to invalid locations. DNS-Based Black Lists (DNSBLs) can also help thwart crackers attempts to poison a user’s hosts file through social engineering emails. DNSBL isn’t 100% effective because it’s only aware of historically known offender’s originating IP addresses; nonetheless, DNSBL adds value to any Unified Threat Management system.

I also found this website “Free Public DNS” that lists “Free” and “Public” DNS servers with some pretty interesting offerings such as: adult content blocking, blocking of sites that host malware, phishing schemes, drug related sites, aggressive/violent sites, and sites known for distributing botnets. They also list both primary and secondary DNS servers. Primary DNS servers have read/write access to the resolution database while the secondary DNS server has read-only access to the database. The secondary DNS server can only receive updated records from the primary DNS server.
OpenDNS offers a plan called “Family Shield” that blocks adult content, among other things, at no cost. OpenDNS also offers a VIP package starting at $19.95/yr which offers faster and more reliable internet connections in addition to parental controls, anti-fraud, and phishing protections. This website “SecSpider” polls for DNS Servers that have deployed the DNSSEC protocol and some of the results are surprising to me. OpenDNS has a Home Parental Control plan that blocks all of the unthinkable sites that kids may be curious about. They also offer customizable filtering options. “Home Parental Controls”.
Intranet Security
The number one security mechanism I would put in place to protect the intranet is educating users on proper use. Each user needs to be aware of how, when, why, and where they log into the intranet. Logging into an intranet using an insecure connection could potentially put the entire intranet at risk if malware or a Trojan were to be implanted. Every user should also be assigned a PIN and/or a username password combo that should be of good quality. This added layer of security ensures that users only have access to areas they have permissions for. All transactions should also be confirmed to ensure they are valid. Confirmations legitimize a transaction by sending a response and recording the event.
One of the most important, least considered and overlooked security mechanisms is physical control. The location that houses the intranet server/servers needs to be inside of a secured facility with proper access privileges in place. Limited access to authorized individuals helps assure computers and/or devices are not removed. Sensitive webpages should be encrypted with SSL. SSL encrypted web pages allow organizational employees to view sensitive data securely over the Internet such as 401Ks and payroll information.
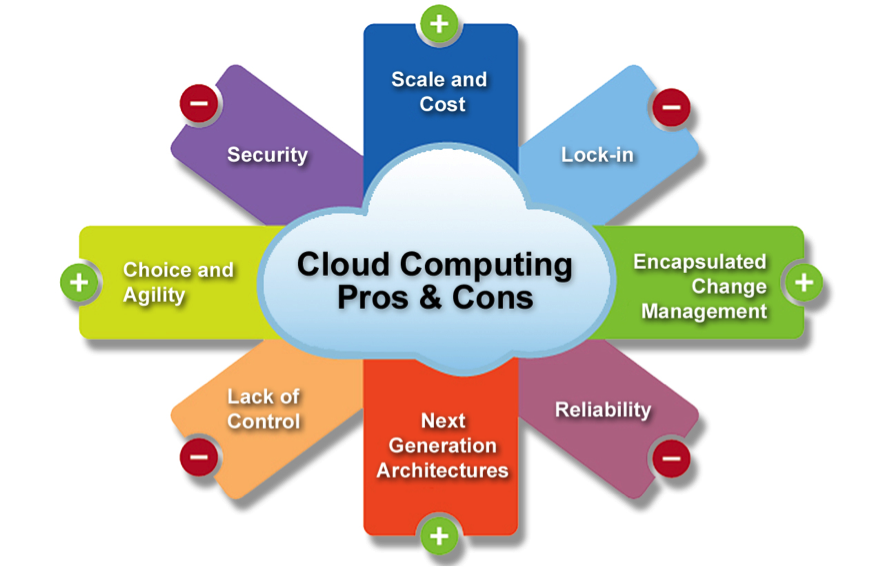
Cloud Computing
Cloud computing is quite simply described as the delivery of on-demand IT resources and applications that are provided over the internet through the use of subscription based services. I will highlight the framework around the benefits of using cloud based services as well as the strategies involved in risk mitigation to assist in the successful use of this service. Cloud computing has the ability to transform massive areas of information technology, is highly regarded as the future of computing, and is seen as a way for businesses to massively cut network and computing expenditures. The ability for consumers, who use cloud infrastructure, to benefit from using bleeding edge technology at extremely lower costs, without the need to purchase said infrastructure and maintain it, is insurmountable. This in a sense levels the playing field for small business affording them the same opportunities for which was previously held only by large corporate conglomerates. In a simple analogy, cloud computing can be thought of as a type of “Leased Network” where you pay for the use of an entire network residing in the cloud.
The outsourcing of software applications are known, in cloud computing terms, as Software as a Service (SaaS), which has the capability of providing the use of software applications running within the confines of cloud infrastructure. These software applications are accessible from a wide variety of resources including; Web browsers, program interfaces, email programs, and other thin client interfaces from virtually any computer connected to the Internet. I would consider outsourcing software to a cloud provider due to significant cost savings that can be realized in lower fees associated with subscription-based services. SaaS’s infrastructure is maintained within huge datacenters owned and operated by the cloud provider. The costs associated with maintaining hardware, software upgrades, software security patches, physical security, and personnel, is absorbed by the cloud provider. The infrastructure used to support all cloud-based services are based upon shared resources that all of the cloud providers utilize simultaneously.
Cloud Computing Service Models
Software as a Service (SaaS). Consumers utilize applications running on a cloud infrastructure, which is accessible through various client devices including; thin clients, web browsers, and program interfaces. Consumer don’t have the ability to manage or control the underlying cloud infrastructure including; servers, operating systems, storage networks, and individual application features. SaaS is typically subscription-based services that’s paid monthly.
Platform as a Service (PaaS). Consumer-created infrastructure or applications using programming languages, services, libraries, and tools maintained by the cloud provider. Consumers don’t have the ability to manage or control the underlying cloud infrastructure including; servers, operating systems, or storage networks, but do control the deployed application and potentially the configuration settings for the hosting-application ecosystem.
Infrastructure as a Service (IaaS). Infrastructure provided to the consumer who has control to: provision processing, design networks, build storage, and control any other underlying computing resources for which the consumer is able to deploy and run arbitrary software for, including operating systems and associated applications. The consumer doesn’t have the ability to control the underlying cloud infrastructure. The consumer does have the ability to control operating systems, storage, and deployed applications with the limited possibility to control select networking components, i.e. firewalls.
Deployment Models
- Private Cloud: Infrastructure designed for the sole use by a single organization that may be owned, operated, and managed by the organization, third party, or any combination.
- Community Cloud: Infrastructure designed for community use of specific organizations with shared concerns, i.e. Security policies, operations, and compliance considerations. It may be owned, operated, and managed by the organization, third party, or any combination.
- Public Cloud. Infrastructure designed for open use by the general public, which may be owned, managed, and operated by a government organization, academic entity, business, or any combination thereof. It’s origins lie within the confines of the cloud provider.
- Hybrid Cloud. Infrastructure designed as a composition of two or more distinct cloud models. The entity remains unique but share standards and proprietary technologies, which enables data and application portability, i.e. cloud bursting for load balancing between clouds.
Costs Savings and Cloud Security
SaaS’s model is based on the Mind Your Own Business (MYOB) methodology. This essentially tells businesses you no longer need to worry about hiring an expensive team of IT experts to design, manage, and maintain an exorbitantly costly network and its associated hardware. Each cloud provider has their own service level agreements, which may or may not contain specific provisions related to the security needs of the business. There could possibly be security gaps in end user agreements that carefully need to be considered. Entrusting data management to the cloud provider including regular back-ups and other maintenance issues takes control away from the company, who has no control over the policies and procedures used to do so by the cloud provider. One of the major concerns related to migrating to cloud based services is the integrity, security, and privacy of the outsourced data. Policies associated with protecting consumer data may be negotiated with cloud providers but the costs of doing so may not be reflected in the original costs summary, which can be amended.
There is little regulatory framework provided by government institutions due the infancy of cloud based technologies, which further exacerbates consumer worries over data handling by these cloud providers. Alas, the service level agreement is the standing legal regulatory document, which is controlled by the cloud provider and most likely will be written to protect the cloud provider’s interests. As time progresses, cloud providers do have the understanding that major security breaches are not economically viable for their businesses. It’s in the best interests of the cloud provider and consumers to negotiate their service level agreements at a minimum. It is my view that SaaS would allow the perfect balance over security and data protection.
There are many threats that affect all the layers of cloud based services but the most vulnerable one I consider to be the biggest threat is due diligence on behalf of the cloud service provider at the IaaS service layer. Infrastructure as a Service (IaaS) sits at the bottom of the cloud based computing hierarchy, which essentially provides computing power to the rest of the cloud. It is at this layer where virtual machine services are offered to the public. IaaS is an ideal platform for hackers to launch their cracking exploits because all cloud computing subscribers of virtual machines lie within this realm, which are directly linked to service offerings from the cloud computing architecture shared resource pool . The flaw is inherently built into the design of IaaS. In this sense, its greatest selling point is consequentially its greatest weakness. Therein lies the dependence of due diligence on behalf of the cloud provider to successfully officiate a good vulnerability management campaign. Being that cloud services are still in their infancy, there is still the great unknown void of potential vulnerabilities that have yet to be seen. Using a wide variety of hacking techniques, hackers can gain access to databases in cloud environments through hijacking a session or eavesdropping on parallel communications. Cloud computing hypervisors, which conduct administrative services, could potentially be compromised by Zero Day attacks. Once the IaaS service model has been compromised, malware could easily be deployed causing system wide damage. A vast number of online media services utilize cloud-based platforms to deliver service to their subscribers. Netflix uses Amazon Web Service (AWS) to deliver content, which is one the leading online cloud providers. Dropbox, Sendspace, and Yousendit are examples of online cloud storage service who utilize the IaaS service model from cloud service providers. All these services store sensitive information in the cloud making it an attractive target for hackers.
Storage
A business of any size can afford to purchase a Storage Area Network (SAN) and manage them locally, thus, only requiring the need of the SaaS cloud service model for application specific needs. SAN’s typically require minimal knowledge and are cost efficient enough to manage on a small scale by the company. This puts the control over data integrity and privacy back in the hands of the company while still benefiting from the SaaS cloud model. Essentially a data breach at the cloud provider would be limited to the servicing of the application and not actual data loss or compromise; therefore, it is my recommendation to locally manage storage while outsourcing critical software applications.
Conclusion
The ability to monitor network traffic is critical to securing information systems. An IDS/IPS deployment is instrumental in helping secure critical networks. The Intrusion Prevention System is capable of using signatures to detect anomalies in traffic to help prevent attacks such as denial of service. Businesses need to carefully consider the costs associated with network breaches against the costs of securing a network and establish budgetary guidelines accordingly. For a business to be successful in today’s economy, it must maintain an online presence and open up it’s network to the world. This in itself is where the vulnerabilities lie and a prudent network administrator should make network security a top priority. Without significant capital investment, businesses can provision cloud based network services on a scalable level suited to their specific needs. All cloud-based services including: compute, networking, storage, database, application, deployment, and management services are scalable, which in effect allows businesses to grow at a much more affordable pace than before. Cloud based service delivers powerful resources at low operational costs. MYOB allows consumers to focus on the core needs of their business enabling them to deliver products and services to market faster and more efficiently than ever before.
Sources
Network and System Security, 2nd Edition By: John R. Vacca
http://www.workforce.com/articles/10-ways-to-protect-intranet-data
Nicholas Pappas, SANS Institute 2008, http://www.sans.org/reading-room/whitepapers/intrusion/network-ids-ips-deployment-strategies-2143
http://www.sans.edu/research/security-laboratory/article/372
Amazon Web Services. (2015). Amazon.com. Retrieved 4 26, 2015, from What is Cloud Computing?: http://aws.amazon.com/what-is-cloud-computing/
Grance, P. M. (2011, 9). NIST PUB 800-145. Retrieved 4 25, 2015, from http://faculty.winthrop.edu/domanm/csci411/Handouts/NIST.pdf
Michael Armbrust, A. F. (2009, 2 10). Above the Clouds: A Berkley View of Cloud Computing. Retrieved 4 26, 2015, from http://ftp.cs.duke.edu/courses/cps296.4/compsci590.4/fall13/838-CloudPapers/AboveTheClouds.pdf
Millard, K. H. (2012, 5 10). The IT Law Community. Retrieved 4 26, 2015, from scl.org: http://www.scl.org/site.aspx?i=ed28054
Ogan M. Yigitbasioglu, K. M. (2013, 8). The International Journal of Digital Accounting Research. Retrieved 4 26, 2015, from http://www.uhu.es/ijdar/10.4192/1577-8517-v13_4.pdf
Rackspace. (2015). What is Cloud Computing? We help break it down. Retrieved 4 26, 2015, from Rackspace: http://www.rackspace.com/cloud/what_is_cloud_computing
Discover more from Decentralized Intelligence
Subscribe to get the latest posts sent to your email.