
5 Minutes
In an effort to help identify and classify malware samples, Yara rules have been specifically written to help identify if a computer or system is infected, and if so, uncover the location of potentially infected files.
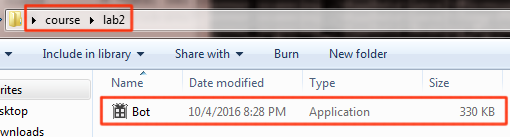
The first Yara rule, as seen below, was written to identify any files and their location on disk that could potentially be infected with the Prosium Bot. The following strings have been optimized to help minimize false positives while providing the most effective file identification possible.

The string “/Digital/prosium.php”, which is indicative and instrumental to the Prosium Bot, is used as part of an http communications stream to send POSTS back to the attacker’s system, information that contains in part some of the following information such as: running processes, network interfaces, and computer / user names. In an effort to circumvent firewalls and/or proxies, Prosium.php communicates across the well-known port 80 in an effort to thwart network defenses.
The bot.pdb file is a “program database” that the debugger uses and indicative that the file was compiled using most likely a C# compiler.
The following string “?controller=api&action=commands&id=” is also indicative of the prosium bot that is used to send commands through an internet connection through the use of PHP scripting.

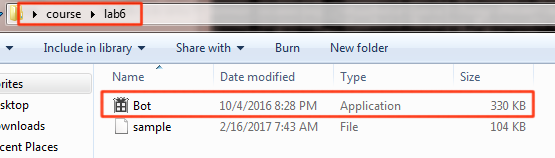
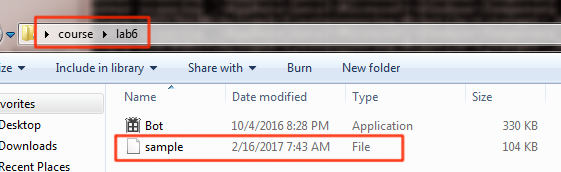
The second Yara rule presented a little more difficulty in in identifying files that were potentially infected with the Ratankba malware. After some research, I can to the conclusion that I had to utilize the IsPE rule to include portable executable as part of the scan. It does this by identifying files with the “MZ” in the PE header by including and analysis of the PE header as part of the scan. Once the private rule IsPE was included I was able to identify all files that of the PE type that included the strings as outlined below.

With the help of the IsPE rule, the following strings help eliminate the number of false positives that I initially returned during my initial scans. The strings “OpenSCManagerA”, “RegSetValueExA”, and “RPCEvent%d” are all indicative of the Ratankba malware.


References
Malwr. (2016, October 4). Network Analysis HTTP protium.php. Retrieved August 13, 2017, from https://malwr.com/analysis/OWUwYmY0ZjRkYTg3NDczZjk5MjNhNWEyODNjZjUxNmE/
Yara. (2017). Welcome to YARA’s documentation! Retrieved August 13, 2017, from http://yara.readthedocs.io/en/v3.6.0/
Payload Security. (2016, November 18). Bot.exe. Retrieved April 13, 2017, from https://www.hybrid-analysis.com/sample/6bd51f44230010e4c435c63364f26188531908035000e747721732f9735c96c1?environmentId=100
Discover more from Decentralized Intelligence
Subscribe to get the latest posts sent to your email.