Abstract
New directions in research have led to fundamental design changes in Wi-Fi technologies, networks, and services. These innovative advances have led to a prolific growth in wireless network computer crimes. As a result, forensic investigators are faced with future challenges associated with consumer’s hunger for high energy consumption, in addition to, issues regarding limited spectrum bandwidth.
Introduction
Wireless devices have become so engrained in today’s society that it’s become hard to imagine life without them, therefore, access to Wi-Fi networks have become ubiquitous. Eighty-seven percent of consumers have in-home Wi-Fi and are willing to engage in high risk behaviors in order to maintain those accesses and although 7 in 10 users desire to improve their Wi-Fi security, only 27% of users actually believe that they will become the victims of a Wi-Fi network breach. (Norton Cybersecurity Insights Report, 2016)1.
Consumers and businesses alike, for the most part, are unaware how of quick and easy it is for criminal hackers to snoop on their communications while acquiring sensitive private information such as: usernames, passwords, bank account numbers, home address, and social security numbers just to name a few. This is why wireless forensics has come to the forefront of many electronic computer crimes and is a growing industry. Organizations need to be prepared to respond and include wireless forensics as part of their incident recovery. Wireless forensics has the capability of yielding a goldmine of information as to how, who, what, when and where an attack occurred, which can help an organization from becoming a repeat victim.
Wireless Forensics
Wireless Forensics’ main goal is to provide a methodology upon which computer forensic scientists can collect and analyze wireless communications that could potentially be used in a court of law as digital evidence.
Overview of the Medium
Wireless technologies are broadly classified as Wireless Local Area networks (WLANs), Wireless Personal-Area-Networks (WPANs), and Wireless Wide-Area-Networks (WWANs) with each technology being determined by the distance of its operation. WLANs typically operate within a few hundred feet which suits applications for home use, as opposed to WPANs, which have an operational range of a few feet. WWANs operate on a larger footprint which typically spans metropolitan cities and/or through intercity links using microwave technology.
Wi-Fi network operate primarily in two distinct frequency spectrums 2.4 GHz and 5 GHz. As seen below in figure 1, the 2.4 GHz Wi-Fi frequency spectrum has 14 distinct channels each at 22 MHz wide.
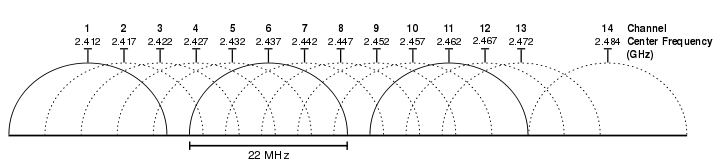
Figure 1
Wi-Fi Technology Overview
802.11
Wi-Fi technologies allow the wireless interconnection of mobile devices through the use of radio waves eliminating the need for hardwires. Of all the wireless technologies today, Wi-Fi is the most prominent and continues to grow at a staggering rate. Several variants of the IEEE 802.11 specification exist and are outlined in figure 2 below.
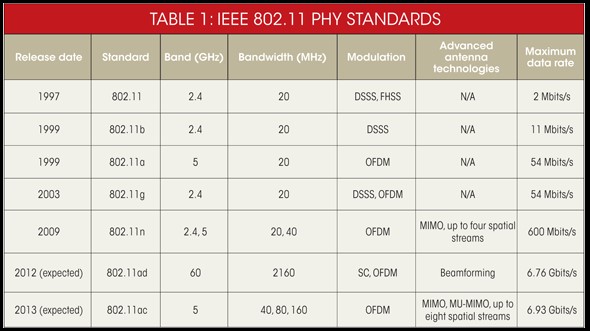
Figure 2
Wireless Access Points
A wireless access point, or WAP, is essentially a unit that acts as a central transmitting unit for all remotely connected wireless devices.
· SSID
WAPs identify themselves with the use of a Service Set ID or SSID, which is a unique 32 alphanumeric character ID specific to that WAP. SSIDs, which is a name given to the network, usually acts as a password when remote devices attempt a connection to the WAP. SSIDs are also what differentiates one Wireless network from another making wireless network management easier.
· BSSID
Basic Service Set Identifier is typically the hardware MAC address assigned to the wireless network interface. The BSSID cannot be changed as it burned into the chipset during the manufacturing process but with the advent of modern software, it can be spoofed and/or altered locally and remotely.
RFID
Radio Frequency Identification technology is prevalent in the retail industry and has recently seen an explosion in warehousing and merchandising. RFID technology can also be found in FasTrak and E-ZPass used in cars for toll bridge crossings. RFID is an automatic identification technology AIT, which uses radio waves to initiate automatic data acquisition. There are three basic types of RFID:
- Active RFID: Battery powered that provides a partial or complete source of power to the RFID tag’s circuitry and antenna.
- Passive RFID: Does not contain a battery. Receives power from the reader itself. When the reader gets close enough to the tag, radio waves from the reader pass to the RFID tag and generates an electromagnetic current from which the RFID tag draws its power, thus, energizing the RFID tag.
- Battery Assisted Passive (BAP): Hybrid of both active ad passive types that contains its own integrated power source, which can retrieve energy from reader to awaken up the chip.
RFID attacks do occur but typically require high end equipment to acquire data from a long range since RFID is a low power short range technology. RFID technology is susceptible to some of the most well known types such as:
- Reverse Engineering: Required the physical acquisition of the chip to later be dismantled by the attacker.
- Power Analyses: This attack occurs through the use of energy harvesting tactics performed by monitoring power consumption levels of RFID power emissions.
- Eavesdropping & Replay: Requires the use of an unauthorized RFID reader, which is used to sniff communications between two linked RFID devices. This technique requires the hacker to have knowledge of RFID protocols and specific tag & reader information.
- Denial of Service: Attacks performed by sending jamming signals with noise interference, removing and/or disabling tags, or blocking RFID radio signals entirely.
Bluetooth
Bluetooth is a low energy, wireless radio, close range technology that can be found in everything from Computer keyboards, Mice, speakers, clocks, and wearable’s such as, watches, Fit Bits, headphones, etc… There exists two prevalent implementations of the Bluetooth specification as flows:
- Bluetooth with low energy functionality (LE): Initiates long range radio communications through short range bursts. Used most frequently in IoT applications that rely on extended battery life and do not require a continuous connection. Operates at a max distance of 330ft, over the air data rates 125kbit/s, 1Mbits/s, 2Mbits/s, uses 128-bit AES with Counter Mode CBC-MAC security, adaptive frequency hopping, 24-bit CRC, 32-bit Message Integrity Check, Peak current consumption <15mA.
- Bluetooth BR/EDR: Continuous connection at short ranges. Used mainly for audio streaming. Operates at a max distance of 330ft, data rates 1-3Mbits/s, Adaptive fast frequency hopping, FEC, fast ACK, Peak current consumption <30mA.
- Dual-Mode: Hybrid chipset, typically found in mobile devices that allow connections to both BR/EDR devices like headsets and LE devices like wearables.
There three most prominent Bluetooth attacks that can occur are:
- Bluejacking: A relatively harmless attack that can create confusion for the user during an attack. A criminal hacker would send unsolicited messages to Bluetooth devices within range, which are most commonly sent as text but can also be sent as sounds or images.
- Bluebugging: Attackers take over the mobile device then snoop in on the conversation allowing the ability to perform the same commands as the user i.e., send messages, activate call forwarding, etc..
- Bluesnarfing: Any unauthorized access to or information theft of an established Bluetooth connection providing attackers access to information such as: calendars, email, text messages, and contact lists.
Bluetooth keyboards are a popular target for attacks where a criminal hacker could quite easily steal user login credentials such as medical and banking usernames and passwords. There are primarily two methods upon which this can be done.
- Hardware Keylogger: Require the attacker to have physical access to the cable connection between the keyboard and the computer. Records all keystrokes then sends to a text file which can be parsed at a later time at a remote location. Stealthier of the two methods because hardware Keyloggers utilizes their own computing resources thus circumventing any IDS alert messages.
- Software Keylogger: Usually malware that’s installed by an attacker which lies resident on the local machines hard drive or in memory. Less stealthy as it utilizes local machine resources and may trigger an IDs alert.
Wireless Forensics Checklist
Radio Frequency Interfaces
· Direct-sequence spread spectrum
2.4 GHz band up to seven channels of 1or 2 Mbps. Each bit of the original signal is subdivided into multiple bits in the transmitted signal, referred to as “Chipping Code”. Chipping Code algorithms spread the original signal across a wide frequency band in direct proportion to the amount of received bits, in essence, a 10-bit chipping code would spread a signal across a frequency 10 times larger then a 1-bit chipping code.
· Frequency Hopping spread spectrum
2.4 GHz band at data rates 1 Mbps and 2Mbps, typically operates with the ISM bands (industrial, scientific, and medical), therefore, forgoing FCC license requirements in the United States. Signals are broadcast over a randomized series of radio frequencies, in essence, hopping across various frequencies within a fixed interval. The receiver, which is synchronized with the transmitter, receives intelligible information while potential attackers hear gibberish. Jamming attempts disrupts only a few bits at a time.
Attributes of Wi-Fi services
- Association: Initial process of association between an AP and station within a specific BSS.
- Re-association: The process of transferring access from one AP to another that allows any particular mobile station to move freely between any BSS.
- Disassociation: The process of terminating a station’s association with an AP.
- Authentication: Process of stations establishing identities with one another.
- Privacy: Used to maintain confidentiality of transmitted messages. Encryption may or may not be used.
Global Position System
GPS metadata artifacts can be found in almost everything digital such as: photos, music download files, automobile satellite navigation units, etc… GPS also provides outdoor locations, accurate timestamps, and valuable GPS log information.
Packet capture
Data packets contain the raw data referred to as the payload within a communications stream. Data packet headers contain routing headers, which also contain critical routing information such as source and destination IPs. Packet captures are used to identify security flaws and/or breaches by determining the origin of intrusion, identification of data leakages, troubleshooting undesired events, Identifying packet/data loss, and forensically by allowing network defenders to understand the extent of the issue.
Radio Signal Strength
Wi-Fi radio signals are measured in dBm or Decibel per milliwatt. Signal strength play s a role most particular in the type of application being used, for instance, -70dBm is adequate enough for sending emails, scanning barcodes, or surfing the Internet. -67dBm is sufficient for higher-throughput applications such as voice over IP, voice over WiFi, and streaming video. Mobile devices typically operate within -65dBm.
Wireless Forensics Toolkits
Pcap format capture
PCAP, or Packet Capture, is the predominant traffic capture format available today. Wireshark is the most popular tool designed for packet capture analyses. Wireshark is a highly efficient protocol analyzer that is the equivalent of a microscope allowing users to dive deep within the packets and uncover critical details required during a forensic investigation. PCAP files are flexible and can be found on both Linux systems as libpcap and Windows systems as WinPcap files. Wireshark also work on both systems as well and freely downloadable from the Internet as an open source tool supported by a massive community of experts located around the world.
Wi-Fi Pineapple
WiFi Pineapple is a wireless auditing tool designed scan, target, intercept, report, record, and analyze logs. The WiFi Pineapple is highly portable and can be used as a man-in-the-middle device, rogue AP, device tracking and alerting, and performs flawlessly during WAR driving.
Aircrack-ng & KISMET
Aircrack-ng is an 802.11 WEP and WPA-PSK key cracking tool designed to uncover keys after enough data has been captured. Aircrack-ng is a multi function tool that performs many duties including: configuring fake APs, cracking wireless passwords, decrypting WEP/WPA/WPA2 pcap files, discovers wireless driver information, and much more.
KISMET is a wireless sniffer, network detector, and intrusion detection system. Works predominantly with 802.11 Wi-Fi with the capability to expand, via plug-ins, to accommodate other network types. Work with standard pcap files and is compatible with Wireshark.
fl0p – passive Layer 7 flow fingerprinting
fl0p is a simple passive layer 7 fingerprinting TCP/UDP/ICMP packet sequence flow analyzer. It’s designed to analyze the exchange between clients and servers relative to their layer seven payload sizes and transmission intervals irrespective of content inspection. Subsequent matches are made against a pre-existing database of traffic pattern signatures to ascertain any facts of interest about the captured traffic. fl0p has the ability to peek into cryptographic tunnels and differentiate between human and robotic communications.
Conclusion
Digital forensics is the process of collecting data that has the potential to serve as evidence in a court of law; therefore, maintaining integrity of that data is vital before, during, and after an investigation and should be the mindset of a digital forensic team. Digital forensic teams also need to pay particular attention to all legal considerations during an investigation, such as, unauthorized eavesdropping, which has the potential of rendering all digital forensic evidence inadmissible in court.
Wireless forensics requires attack data that is either captured during an attack, through continuous monitoring, or from an unexpected attack using previously captured log data. Organization’s most typically view encryption as a burden, which in the end may be viewed as an inconvenience to the organization but serves as an added layer of protection. Forensic investigators to be mindful of the organization’s culture which could serve to jeopardize an investigation as well.
Wireless airspace is open to any and all users who so happen to be close enough to pick up a wireless access point’s radio signals, and as result, have the ability to steal, snoop, or spoof sensitive private information. The Wi-Fi Pineapple discussed in this report is one such device available to the public at a low cost, which happens to be one of the most popular WAR driving devices available today.
Unfortunately, the same tools and technologies used for wireless forensics discussed in this report are the same tools used by the bad guys and they know how to use them well in many cases. As is the case with WAR driving, various other means of rogue communications will most certainly continue to serve to both protect and harm users as the perpetual growth of wireless infrastructure continues into the future.
References
[1] Symantec Corp. (2017). 2016 Norton Cybersecurity Insights Report. Retrieved March 15, 2017
[2] Wekhande, V. (2006). WI-FI TECHNOLOGY: SECURITY ISSUES. Retrieved March 24, 2017
[3] Symantec. (2010, November 2). Wireless Forensics: Tapping the Air – Part One. Retrieved March 24, 2017, from https://www.symantec.com/connect/articles/wireless-forensics-tapping-air-part-one
[4] Wi-Fi Alliance. (2017). Wi-Fi Specifications. Retrieved March 24, 2017
[5] Mohaptra, S. K., Choudhury, R. R., & Das, P. (2014, September). The Future Directions In Evolving Wi-Fi Technologies, Applications and Services. Retrieved March 24, 2017, from
[6] Sridhar, T. (2008, December). Wi-Fi, Bluetooth and WiMAX – The Internet Protocol Journal, Volume 11, No. 4. Retrieved March 24, 2017, from http://www.cisco.com/c/en/us/about/press/internet-protocol-journal/back-issues/table-contents-42/114-wifi.html
[7] CISCO. (2014, March). 802.11ac: The Fifth Generation of Wi-Fi. Retrieved March 24, 2017
[8] Wright, J., & Cache, J. (2015). Hacking exposed wireless wireless security secrets & solutions. New York, NY: McGraw-Hill.
[9] Messier, R. (2014). Chapter 14: Wireless Technologies. In GSEC GIAC security essentials certification: All-in-one: Exam guide. New York: McGraw-Hill Education.
[10] Dobrotka, D. (2009, November). Intrusion detection on wireless network? Retrieved April 12, 2017, From https://www.sans.org/security-resources/idfaq/intrusion-detection-on-wireless-network/2/24
Discover more from Decentralized Intelligence
Subscribe to get the latest posts sent to your email.

Pingback: What Are the Branches of Digital Forensics? - Asktohow
Great information! Thanks
LikeLike