5 Minutes
This purpose of this document is to examine the results of several Wireshark captures. Areas to be explored are the exploit type, impact of the exploit, vulnerability type, and any other relevant information. In order for network administrators, penetration testers, or any other type of security experts to combat cyber crimes, it’s critical that they know how to use the same tools that the criminals do. Wireshark is instrumental in helping security professionals dissect intersected communications to formulate new security policies and put new safeguards in place. This experiment will be conducted on a 2009 Mac Pro running OS X Yosemite 10.10.4. Kali Linux will be used to exploit Metasploitable 2 both of which are running inside of Parallels 10 virtual machines.
Procedure
Port Scan
Port scanning is a technique used by security professionals and cyber criminals alike to identify any existing vulnerabilities within a network. The port scan’s main goal is to see whether a TCP port is open, closed, or blocked. This information is invaluable to an attacker because they can potentially gain unauthorized access into an unsuspecting network stealing valuable sensitive data.
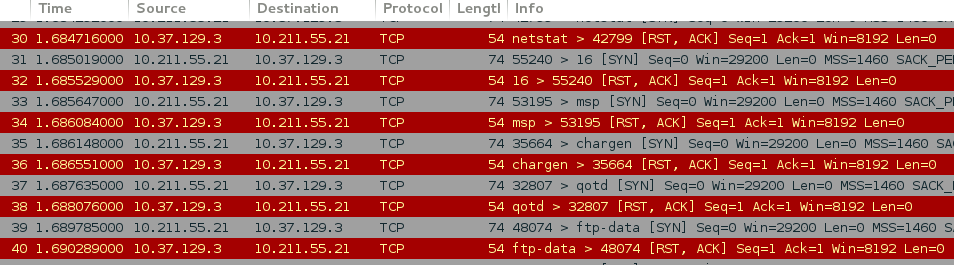
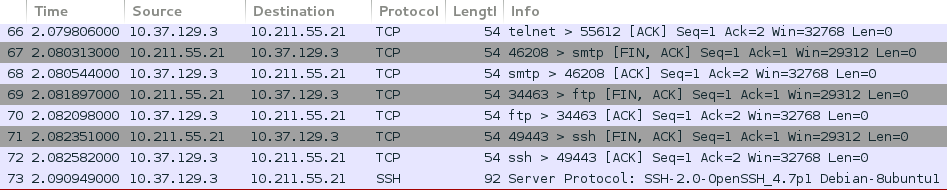
A TCP port scan sends hello packets to a specified number of ports as entered in the search. When a client returns an “RST, ACK” packet, it’s a clear indication that the port is closed as seen in figure 1 above. When the attacker receives an “ACK” packet from the attacked host, as seen in figure 2 below, this indicates that port is open to connections and vulnerable to exploitations. As a result of the scan, a number of vulnerabilities have been detected and various protocols were identified including, telnet, ftp, and ssh, as seen in figure 2 below, which are potential targets for an attacker.
It must also be noted that although a TCP “SYN scan” performs quicker scans, it’s susceptible to being identified by Intrusion Detection Systems (IDS) and is not very stealthy. As an alternative, the “FIN scan”, as seen in figure 2, is the preferred method to help avoid being detected by an Intrusion Detection System. FIN scans work at a much slower pace than SYN scans to help avoid detection. FIN scans may be able to sneak through certain non-stateful firewalls and packet filtering routers. This type of scan is a little more stealthy than a SYN scan but most modern IDS systems can possibly be configured to detect them. The risks associated with port scans include, crashing the host system, and various legal issues. It’s critical for penetration testers to have legal authorization prior to performing these tests.
Port scans aren’t necessarily attacks and in most cases don’t cause any harm to the target systems if done properly and without malicious intent. In particular, a TCP (Full-Scan) could crash a system if the source and destination IP’s are the same, which causes a loop that eventually crashes the host. This type of scan is considered malicious because the end resultant is already known. Instead of performing a TCP full scan, a SYN (half-scan) or a FIN scan is the preferred method, which would represent an actual attacker’s method more accurately because of the stealthy nature behind those particular, scans.
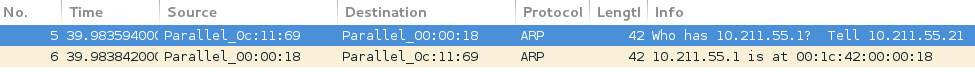
Reverse TCP Connection
A reverse TCP connection is used to allow an attacker from a remote location to have access to a computer through a shell. The attacker sets up a listener on his computer waiting for the target computer to connect to that particular listener, which then allows the attacker access to the command shell. An ARP request is sent out to identify the associated MAC address as seen in figure 3 below.
Cache Poisoning
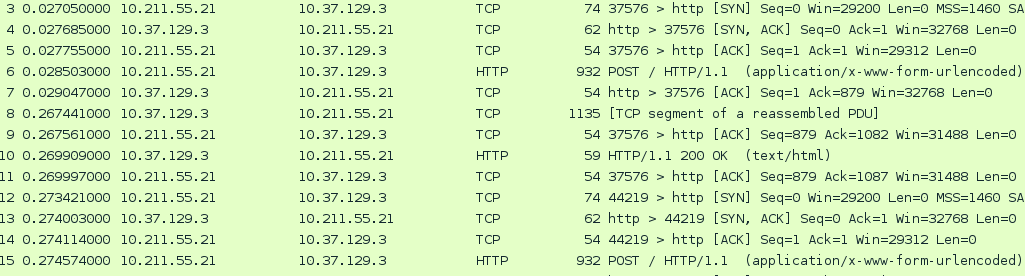
Cache poisoning is a web application vulnerability where an attacker removes and replaces cached webpages in order to deliver malicious content to the user through the use of re-direction. Webpage caching was deigned to help enhance the speed of web browsers. When a user returns to a previously visited web page, it will be recalled from the web browsers cache as opposed to downloading the entire webpage repeatedly. Cache is a specially allocated portion of physical memory.
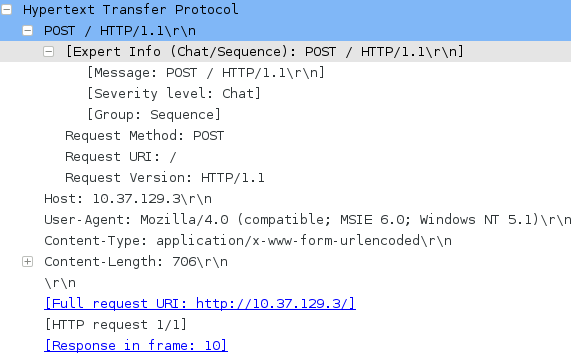
As seen in figure 4, after the successful three-way handshake, the “POST / HHTP/1.1” is a method used to request the originating server to accept the enclosed contents as the new subordinate of the identified resource in the request URI as seen in figure 5 below. Cake PHP, in particular, is prone to remote PHP code-execution vulnerabilities. Attackers inject and execute malicious indiscriminate PHP code within the framework of the affected application.
While Wireshark is only one of many sniffers on the market, it is one the most popular and fully featured packet analyzers. Wireshark is an essential tool to helping network security professionals and black hat hackers alike. Knowing how to use this tool can help mitigate pre-existing network vulnerabilities by identifying weaknesses in computer networks.
Sources
Bradley, T. (n.d.). Introduction to Port Scanning. Retrieved 8 2, 2015, from About Tech: http://netsecurity.about.com/cs/hackertools/a/aa121303.htm
Nmap Reference Guide. (n.d.). Retrieved 8 2, 2015, from nmap.org: http://nmap.org/book/man-port-scanning-techniques.html
tdz, F. W. (2014). CakePHP Cache Corruption Code Execution. Retrieved 8 2, 2015, from Rapid7: https://www.rapid7.com/db/modules/exploit/unix/webapp/cakephp_cache_corruption
Vulnerability Details : CVE-2010-4335 . (2011, 1 22). Retrieved 8 2, 2015, from CVE Details: http://www.cvedetails.com/cve/2010-4335
wchen-r7. (2014, 10 28). How to use a reverse shell in Metasploit. Retrieved 8 1, 2015, from GitHub: https://github.com/rapid7/metasploit-framework/wiki/How-to-use-a-reverse-shell-in-Metasploit
Discover more from Decentralized Intelligence
Subscribe to get the latest posts sent to your email.